Security researcher discovered Zoom installed localhost web server on Macs that persisted after app deletion. Server allowed automatic camera activation bypassing Safari protections.
“This feature is designed to improve user experience by avoiding browser security dialogs when joining meetings.”
From “crazy” to confirmed
The Claim Is Made
This is the moment they called it crazy.
When security researcher Jonathan Leitschuh published his findings in July 2019, he presented evidence of something that seemed almost too invasive to be true: Zoom had installed a hidden web server on Mac computers that remained even after users uninstalled the application. This wasn't speculation or theoretical vulnerability—it was documented, reproducible, and allowed the video conferencing platform to activate users' cameras without their explicit permission in the moment.
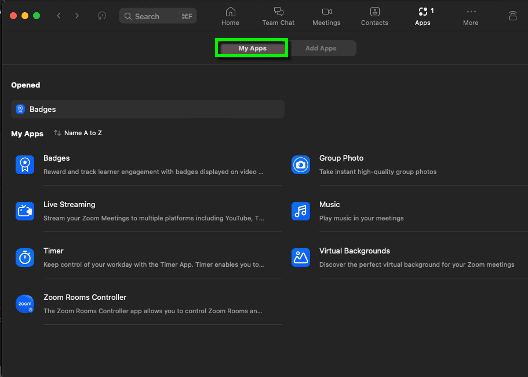
The discovery centered on a localhost web server that Zoom installed during the application setup process. This server persisted on machines even after users deleted the Zoom app from their Applications folder, essentially creating a backdoor that could be exploited. More troubling was what this server could do: it circumvented Safari's built-in protections that normally prevent websites from accessing a user's camera without permission. A malicious website could potentially trigger automatic camera activation through this Zoom server without the user knowing.
When the claim first surfaced, it faced the standard dismissals. Zoom's response suggested that users concerned about privacy were overreacting. The company characterized the persistent web server as a convenience feature designed to make rejoining video calls faster. They explained that reinstalling Zoom would be unnecessary if the server remained available. This framing attempted to reposition a security flaw as a user experience improvement.
But the technical evidence was undeniable. Security researchers could trigger the web server to activate cameras on Mac computers through malicious websites or JavaScript code. The vulnerability wasn't hypothetical—it was functional and exploitable. Leitschuh demonstrated that users had no easy way to remove this server without manual intervention or advanced technical knowledge. The official uninstall process simply didn't remove it.
Faced with this documented vulnerability, Zoom eventually updated its application in July 2019 to address the issue. The company released a patch that removed the persistent web server and required explicit user permission before reactivating camera access in the manner previously available. They also provided a utility to help existing users remove the problematic code from their machines.
What made this situation significant wasn't just the technical vulnerability itself—it was the gap between what Zoom claimed to offer and what the company actually deployed on users' machines. People who installed Zoom believed they were installing a video conferencing application with normal security practices. Instead, they were installing something with persistent system-level access that bypassed standard browser protections.
This incident demonstrated why technical transparency matters in consumer software. Zoom users didn't consent to a persistent web server; they consented to using a video app. The fact that security researchers had to reverse-engineer the application to discover this functionality raises questions about what other software companies might be doing behind the scenes.
The Zoom case became a referendum on trust in the tech industry. It showed that even mainstream, heavily-used applications from established companies could harbor practices that users would find objectionable if they knew about them. The company's initial dismissal of concerns, followed by the eventual patch, suggested that only public pressure and documented evidence forced accountability.
For those tracking how technology companies actually behave versus how they represent themselves, the Zoom web server case represents an important data point: the discrepancy between user expectations and installed reality, and the role that independent security research plays in making that discrepancy visible.
Get the 5 biggest receipts every week, straight to your inbox — plus an exclusive PDF: The Top 10 Conspiracy Theories Proven True in 2025-2026. No spam. No agenda. Just the papers they couldn't hide.
You just read "Zoom App Secretly Installed Hidden Web Server on Mac Compute…". We send ones like this every week.
No one's said anything yet. Be the first to drop your take.





