Der Spiegel revealed NSA's ANT catalog showing how agency intercepted Cisco router shipments to install surveillance backdoors. Photos showed NSA employees opening sealed packages before delivery.
“Our products do not contain backdoors and we do not work with any government to weaken security”
From “crazy” to confirmed
The Claim Is Made
This is the moment they called it crazy.
When security researchers and privacy advocates began suggesting in the early 2010s that government agencies might be intercepting computer equipment before it reached customers, they were dismissed as paranoid conspiracy theorists. The idea seemed too brazen, too difficult to execute at scale, and too risky if discovered. Major tech companies denied such interference was possible. Intelligence officials offered no comment, which most took as reassurance.
Then in 2013, Der Spiegel published photographs that changed everything.
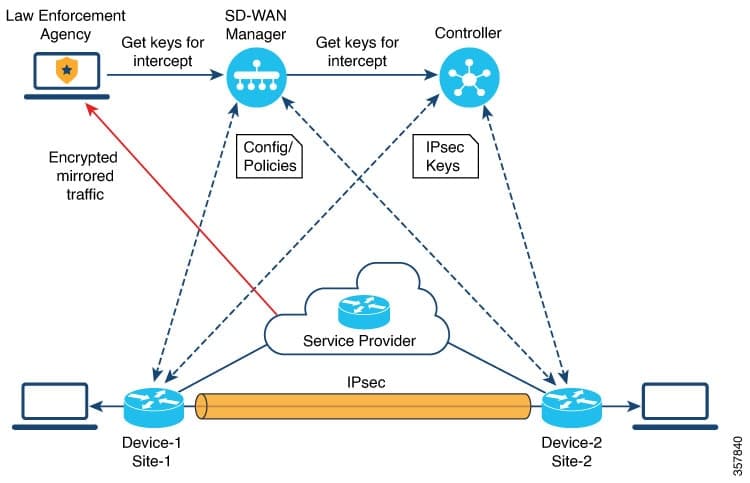
Working from documents provided by Edward Snowden, the German newspaper revealed the existence of the NSA's ANT catalog—a shopping list of surveillance tools available to the agency's Tailored Access Operations division. But the catalog wasn't just about software exploits or hacking techniques. It detailed how NSA operatives physically intercepted Cisco router shipments, opened sealed packages, installed backdoors that would allow remote surveillance, and resealed them for delivery to unsuspecting customers and organizations.
The photographs were damning. They showed NSA employees in what appeared to be a warehouse or mail facility, working on computer equipment that had been diverted from normal shipping channels. The catalog itself listed specific Cisco models and other networking hardware, complete with prices and installation fees. This wasn't theoretical—it was operational procedure, documented and budgeted like any other intelligence program.
The NSA's initial response followed a familiar pattern. Officials claimed the revelations were overblown and taken out of context. They suggested the program was narrowly targeted at foreign adversaries and legitimate threats. When pressed, they acknowledged some version of the activity existed but framed it as necessary counterintelligence work. No apology was offered. No policy changes were immediately announced.
Get the 5 biggest receipts every week, straight to your inbox — plus an exclusive PDF: The Top 10 Conspiracy Theories Proven True in 2025-2026. No spam. No agenda. Just the papers they couldn't hide.
You just read "Cisco Routers Were Secretly Intercepted and Modified by NSA". We send ones like this every week.
No one's said anything yet. Be the first to drop your take.
What made this claim verifiable wasn't just Snowden's documents or Der Spiegel's reporting. It was the internal consistency of what was revealed. The catalog included specific product models, pricing structures, and operational details that fit together logically. Former NSA and intelligence officials, when later interviewed, didn't deny the practice—they justified it. The question shifted from "did this happen?" to "was this appropriate?"
The answer depended on your perspective. If you believed the NSA's narrow interpretation that these modifications only targeted foreign intelligence services and hostile actors, perhaps the practice seemed defensible. But the program's scope remained unclear. How many routers were modified? Which organizations received them? How long did the practice continue? These questions were never fully answered.
What mattered most was the revelation's effect on trust. Cisco and other hardware manufacturers suddenly faced a credibility crisis. How could customers trust that equipment arriving at their doors hadn't been tampered with? Security professionals began recommending customers verify equipment authenticity through multiple channels. International companies, particularly in Europe, became more skeptical of American-made networking hardware.
Years later, this claim's verification exposed a fundamental truth about modern surveillance: the most effective backdoors are physical ones. You don't need sophisticated zero-day exploits if you can simply modify equipment before it reaches its destination. The NSA understood this better than anyone. And for years, they acted on that knowledge while the public remained unaware.
That gap between what government agencies do and what the public knows they do—that gap is what "They Knew" documents.
Beat the odds
This had a 0.7% chance of leaking — someone talked anyway.
Conspirators
~150Network
Secret kept
12.4 years
Time to 95% exposure
500+ years