From STELLARWIND to PRISM to the receipts that keep leaking in 2026.
Edward Snowden didn't start it — he just proved it. This timeline collects every major NSA surveillance receipt, from the Church Committee to STELLARWIND, PRISM, XKEYSCORE and the post-2024 FISA expansions. Everything the government swore wasn't happening.
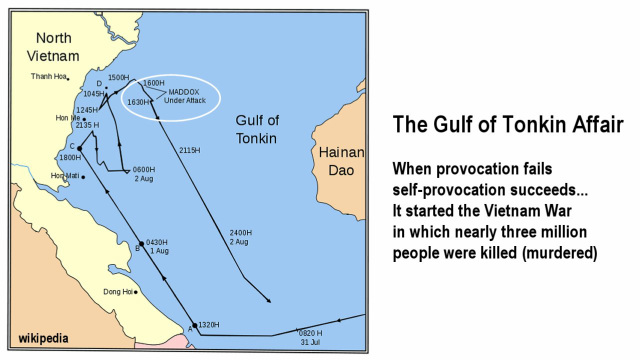
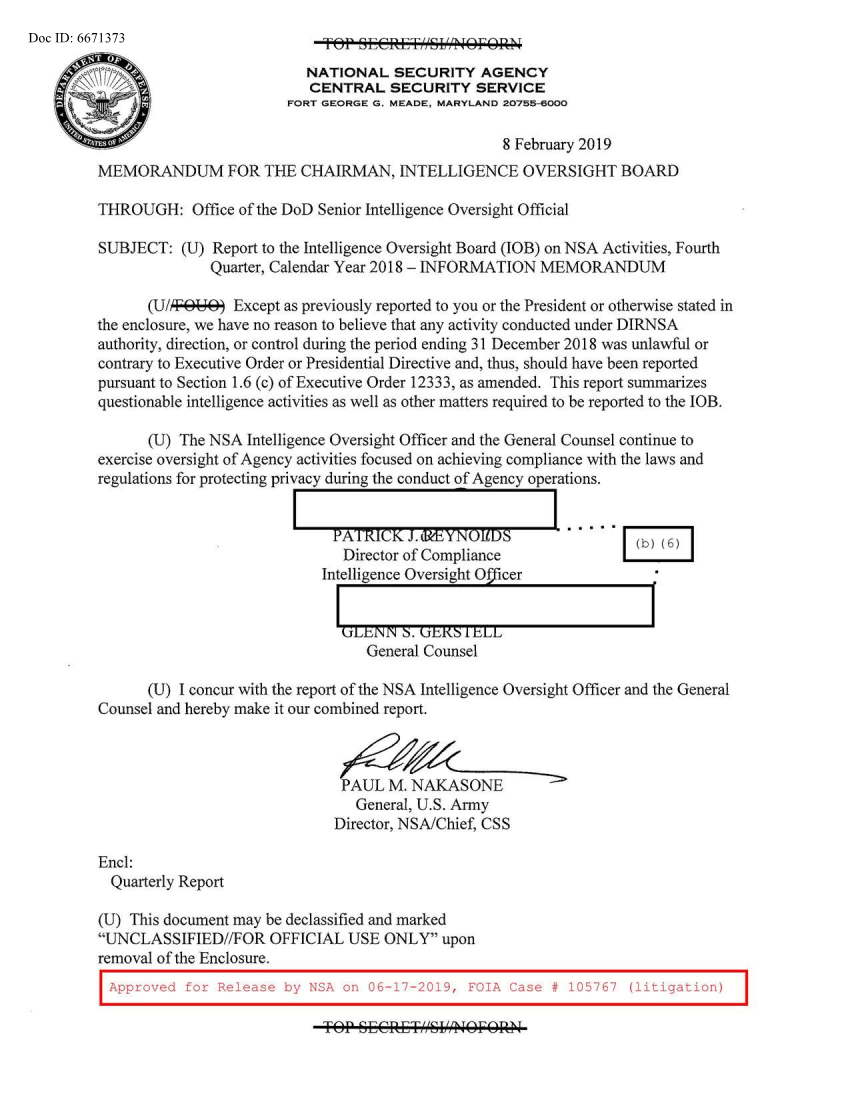
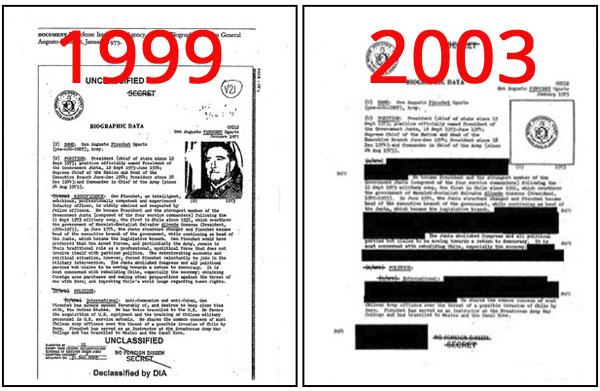
The second alleged attack on August 4, 1964, never actually occurred. Declassified NSA documents in 2005 confirmed that signals intelligence was manipulated to support the claim of a North Vietnamese attack.
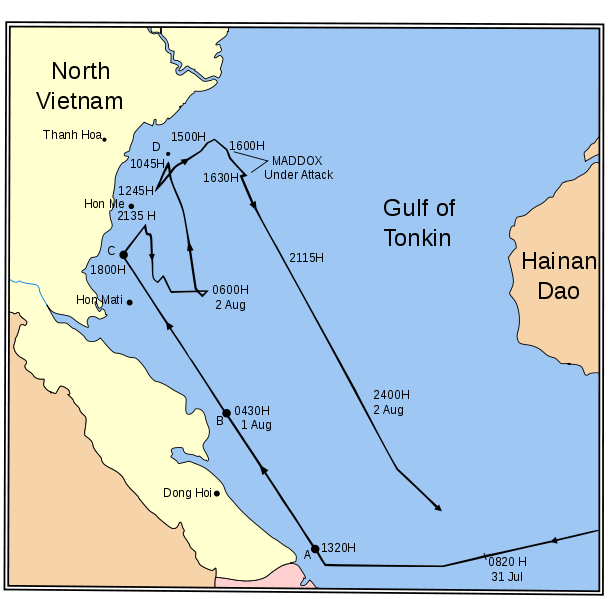
On August 4, 1964, the USS Maddox reportedly came under a second attack by North Vietnamese torpedo boats. President Johnson used this to push the Gulf of Tonkin Resolution through Congress, giving him unlimited military authority. NSA documents declassified in 2005 confirmed the agency deliberately manipulated signals intelligence to fabricate the second attack. Secretary McNamara later admitted the August 4th incident did not occur. The resolution led to the deaths of 58,000 Americans and millions of Vietnamese.
Declassified NSA documents from 2005 revealed that the second Gulf of Tonkin attack on August 4, 1964 never happened. NSA analysts 'made SIGINT fit the claim' of a North Vietnamese attack, deliberately presenting only information supporting the attack narrative to President Johnson. Congress passed the Gulf of Tonkin Resolution based on this fabricated evidence, escalating to full-scale war.
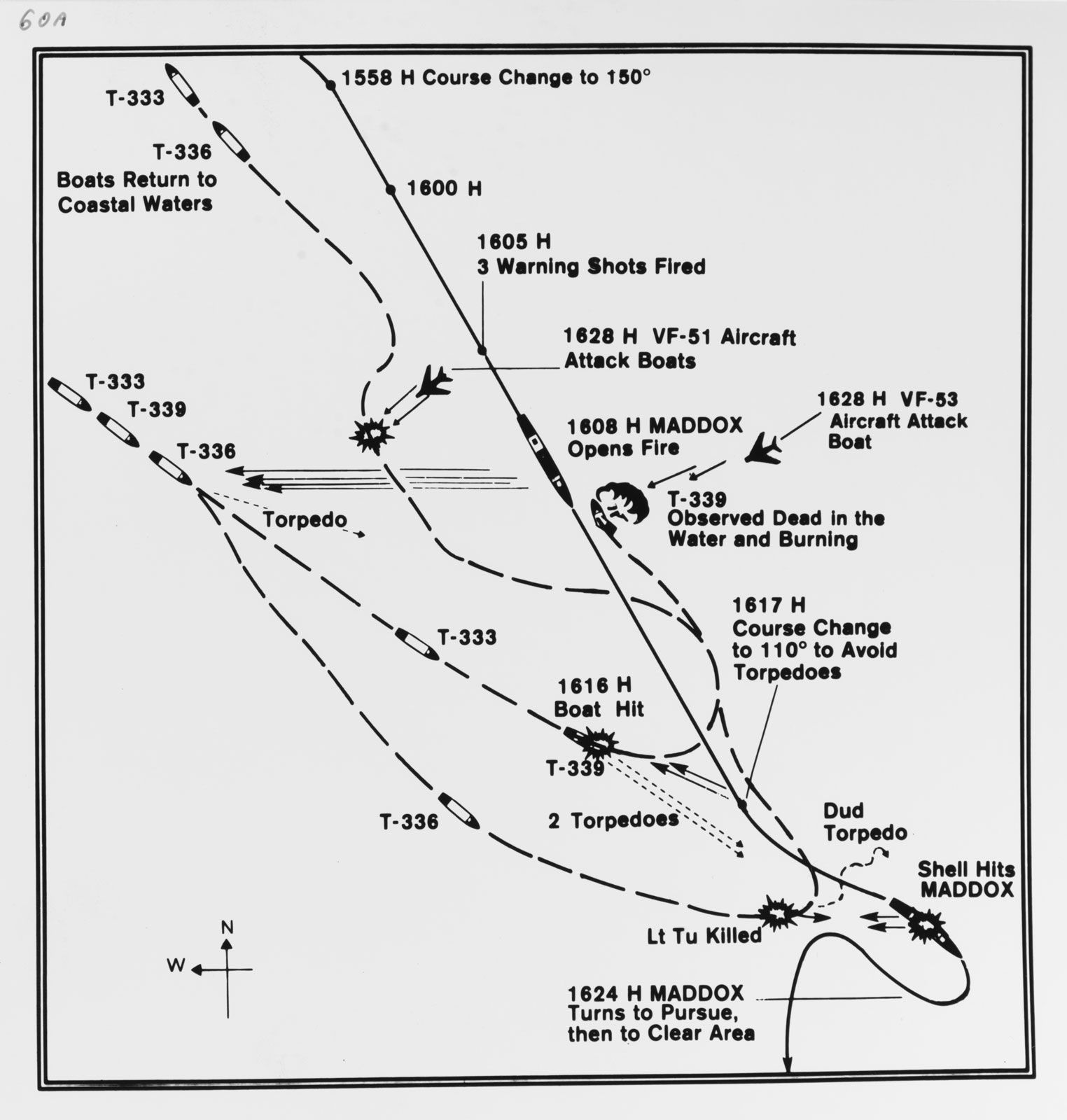
NSA documents revealed the second Gulf of Tonkin attack never occurred. Johnson administration used false reports of North Vietnamese attacks to obtain congressional authorization for massive military escalation in Vietnam.

NSA documents released in 2005 confirmed the second Gulf of Tonkin attack never happened. Officials knew it was false but used it to justify massive escalation in Vietnam.
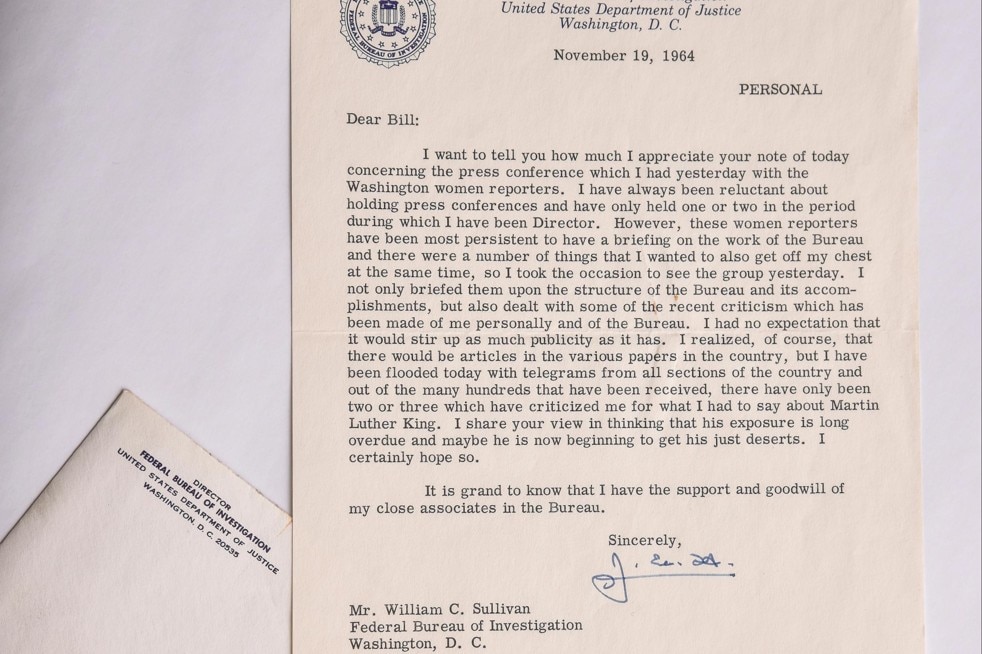
In November 1964, the FBI anonymously mailed Martin Luther King Jr. a package containing surveillance recordings of alleged extramarital affairs and a letter reading: 'There is only one thing left for you to do... You are done. There is but one way out for you. You better take it before your filthy, abnormal, fraudulent self is bared to the nation.' The letter gave King 34 days to commit suicide before the FBI would release the recordings. The letter was declassified in 2014.

On June 8, 1967, Israeli jets and torpedo boats attacked the USS Liberty for over 75 minutes, killing 34 crew and wounding 171. Israel claimed mistaken identity, but survivors insist the ship was clearly marked with a large American flag. Secretary of State Dean Rusk, CIA Director Richard Helms, and Admiral Thomas Moorer all later stated they believed the attack was deliberate. The Johnson administration buried the investigation to protect relations with Israel. NSA intercepts remain classified 50+ years later. The attack likely aimed to prevent the US from discovering Israel's imminent seizure of Syria's Golan Heights.

Israel deliberately attacked USS Liberty in 1967, killing 34 sailors. NSA intercepts proved intentional attack but military covered it up to protect alliance with Israel.

CIA conducted massive domestic surveillance operation from 1967-1974 despite legal prohibition on domestic activities. Church Committee investigations revealed agency compiled files on antiwar activists, opened mail, and infiltrated student organizations.
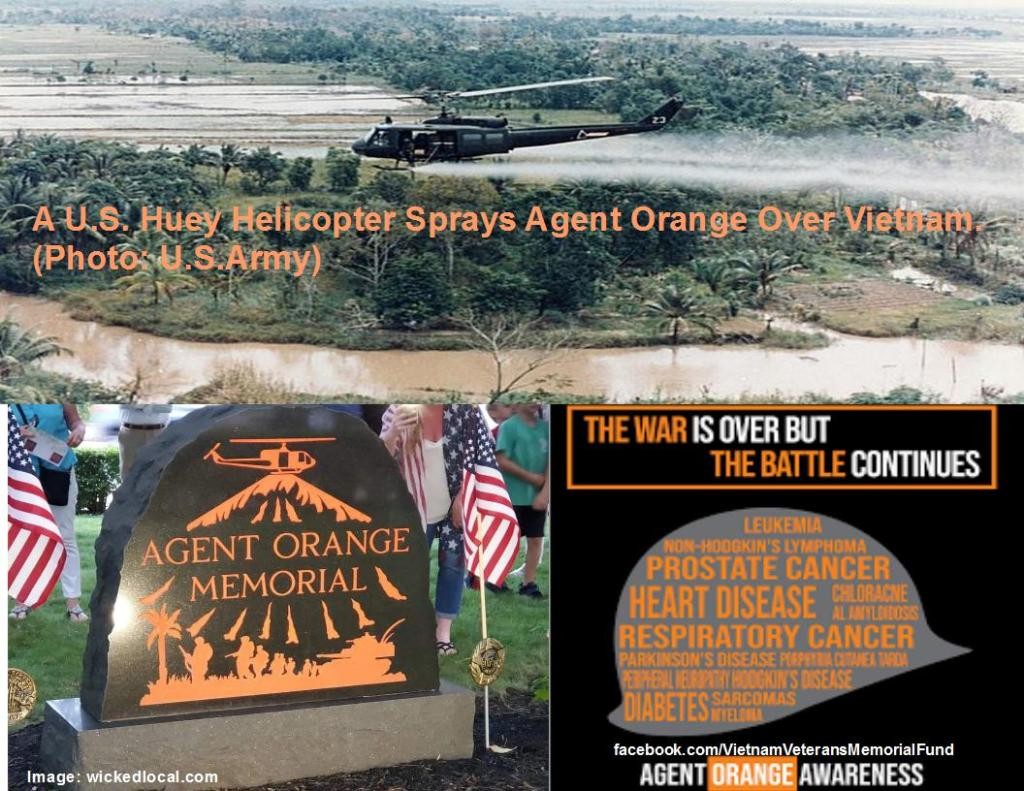
Between 1962-1971, the US military sprayed 20 million gallons of Agent Orange (containing dioxin TCDD) over Vietnam. Manufacturers Dow Chemical and Monsanto knew dioxin was highly toxic. Veterans reporting cancers, birth defects in children, and other illnesses were told their conditions were unrelated. It took until 1991 for Congress to pass the Agent Orange Act, and the VA did not fully recognize presumptive conditions until decades later.

Army Intelligence conducted illegal surveillance on over 100,000 American citizens from 1967-1971. Church Committee investigations revealed massive domestic spying operations targeting protesters.
The FBI denied targeting civil rights leaders, but documents revealed systematic surveillance and disruption of MLK, Black Panthers, and antiwar groups from 1956-1971.
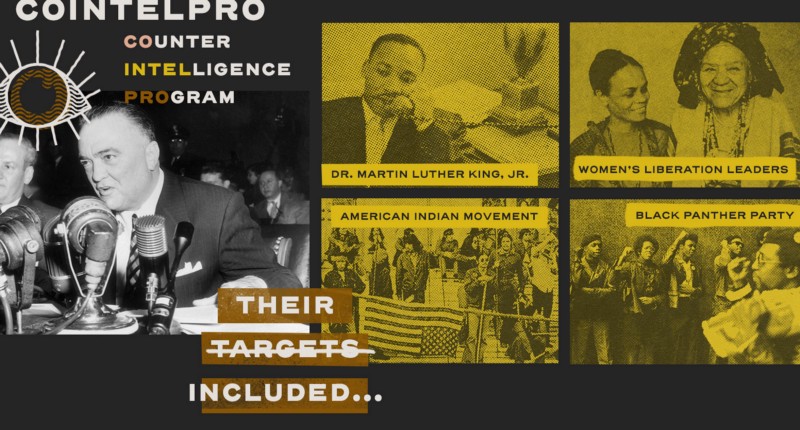
The FBI conducted illegal surveillance, infiltration, and disruption campaigns against civil rights leaders and organizations for decades. FOIA documents revealed systematic violations of constitutional rights.
FBI documents revealed a 15-year program to infiltrate, discredit and disrupt civil rights organizations and political groups. The program targeted everyone from Black Panthers to women's liberation groups through illegal surveillance and sabotage.

The FBI ran a secret program from 1956-1971 to disrupt domestic political organizations through illegal surveillance, infiltration, and psychological warfare tactics.

FBI's secret counterintelligence program targeted MLK, Black Panthers, and other activists with illegal surveillance, harassment, and disruption tactics. Exposed through break-in at FBI office in 1971.
FBI documents revealed systematic surveillance and disruption campaigns against journalists reporting on civil rights and anti-war movements. Operations included break-ins, wiretapping, and planted false stories.
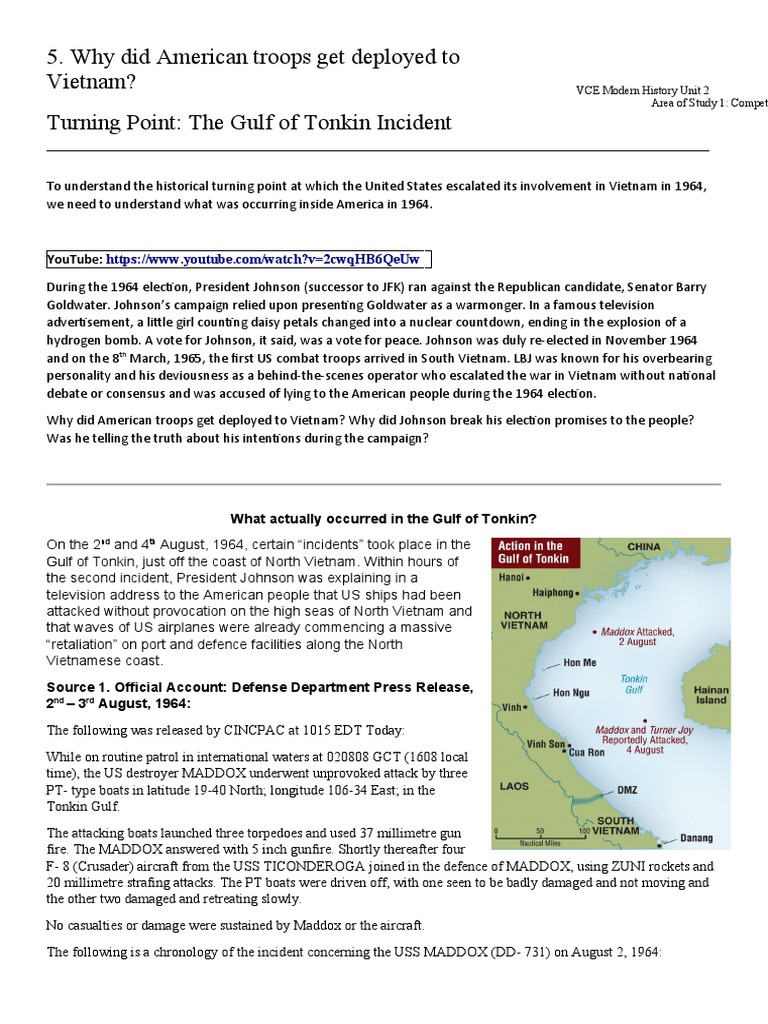
Declassified NSA documents revealed the second Gulf of Tonkin attack likely never occurred, while military officials presented exaggerated and misleading reports to Congress to justify major Vietnam War escalation.

In 1971, the FBI put John Lennon under surveillance due to his anti-war activism, and the Immigration and Naturalization Service attempted to deport him in 1972. Declassified FBI files revealed extensive monitoring of Lennon's activities, phone calls, and associations. The FBI fought for over 25 years to keep the files secret, with historian Jon Wiener suing under FOIA in 1983 and not receiving all files until 2006.

FBI maintained extensive surveillance file on Beatles musician due to his anti-Vietnam War activities. Documents show attempts to deport Lennon and disrupt his concerts and protests.

The Watergate scandal revealed that Nixon's administration engaged in illegal surveillance, campaign finance violations, and obstruction of justice. Nixon resigned in 1974 facing certain impeachment.
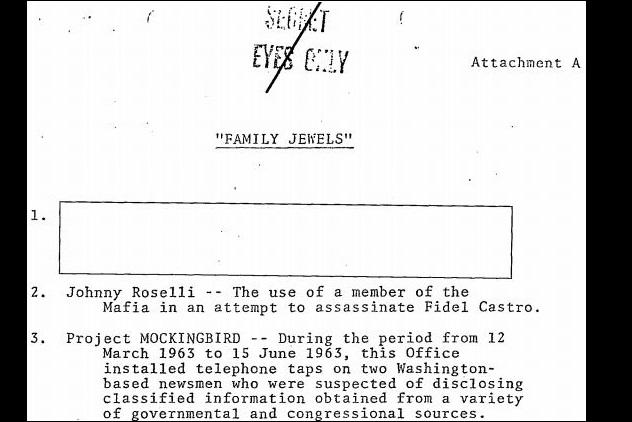
In 1973, CIA Director James Schlesinger ordered CIA employees to report any activities that might have been illegal or exceeded the agency's charter. The resulting 693-page document, known as 'The Family Jewels,' cataloged domestic wiretapping, surveillance of journalists, assassination plots, human experiments, and mail opening. The document was classified until June 2007 when it was finally released under FOIA after 34 years of secrecy.
In July 1973, as part of Operation Wrath of God to avenge the Munich Olympics massacre, Mossad agents shot and killed Ahmed Bouchikhi, an innocent Moroccan waiter, in Lillehammer, Norway -- mistaking him for a Palestinian terrorist. The killing took place in front of his pregnant Norwegian wife. Six Mossad agents were arrested and convicted by Norwegian courts. Israel paid compensation in 1996.
Kerr-McGee plutonium plant worker found radiation contamination and safety violations before dying in car crash. FBI documents revealed company surveillance and intimidation tactics. Autopsy showed sedatives in her blood during supposedly accidental crash.
Operation CHAOS (1967-1974) was a CIA domestic surveillance program that compiled dossiers on over 300,000 Americans, indexed 7,200 citizens, and intercepted mail. The program targeted anti-war activists, civil rights leaders, and journalists. Seymour Hersh exposed it in 1974, and the Church Committee confirmed the CIA had systematically violated its charter prohibiting domestic operations. The program was a direct violation of the CIA's founding statute.

The CIA conducted massive domestic surveillance from 1967-1974, collecting files on 300,000 Americans and infiltrating anti-war groups despite legal prohibitions.

CIA violated its charter by conducting domestic surveillance on 300,000 Americans, infiltrating peace groups and maintaining files on protesters. Program ran from 1967-1974 despite legal prohibitions.

Congressional investigations revealed the NSA conducted domestic surveillance on 300,000 Americans including prominent journalists, violating laws prohibiting domestic spying.

The CIA conducted domestic surveillance operations against American citizens, including journalists covering anti-war protests. Church Committee investigations revealed thousands of files on U.S. reporters and activists.

CIA domestic surveillance program created psychological profiles and monitored communications of war protesters from 1967-1974. Agency maintained files on 13,000 Americans and 1,000 organizations despite having no legal authority for domestic operations.

Senate investigation revealed CIA violated its charter by spying on 300,000 Americans and plotting assassinations of foreign leaders. Operations included mail opening programs, university infiltration, and media manipulation campaigns on U.S. soil.
The NSA conducted domestic surveillance on 75,000 Americans from 1967-1974, including Martin Luther King Jr. and anti-war protesters. The Church Committee exposed this massive illegal operation targeting U.S. citizens.
CIA claimed it operated only overseas, but internal memos documented mail opening, surveillance of Americans, and assassination plots against foreign leaders.
Project SHAMROCK collected millions of telegrams from 1945-1975, while Project MINARET targeted anti-war activists and civil rights leaders without warrants.
NSA secretly obtained copies of all telegrams entering or leaving the U.S. from 1945-1975 through agreements with telegraph companies. Government agencies accessed private communications of citizens with no judicial oversight or legal authority.

Project SHAMROCK (1945-1975) was the largest domestic interception program in history. Major telegraph companies including Western Union, ITT, and RCA secretly provided the NSA with copies of every international telegram entering or leaving the United States for three decades. The Church Committee's exposure of the program led directly to the creation of the FISA courts.

ECHELON, established during the Cold War by the Five Eyes alliance (US, UK, Canada, Australia, New Zealand), grew into a global surveillance network capable of intercepting satellite communications, phone calls, faxes, and emails worldwide. Ground stations at Menwith Hill (UK), Pine Gap (Australia), and other facilities used keyword filters to process intercepted data. The European Parliament concluded in 2001 that ECHELON's existence was 'no longer in doubt' after years of government denials.
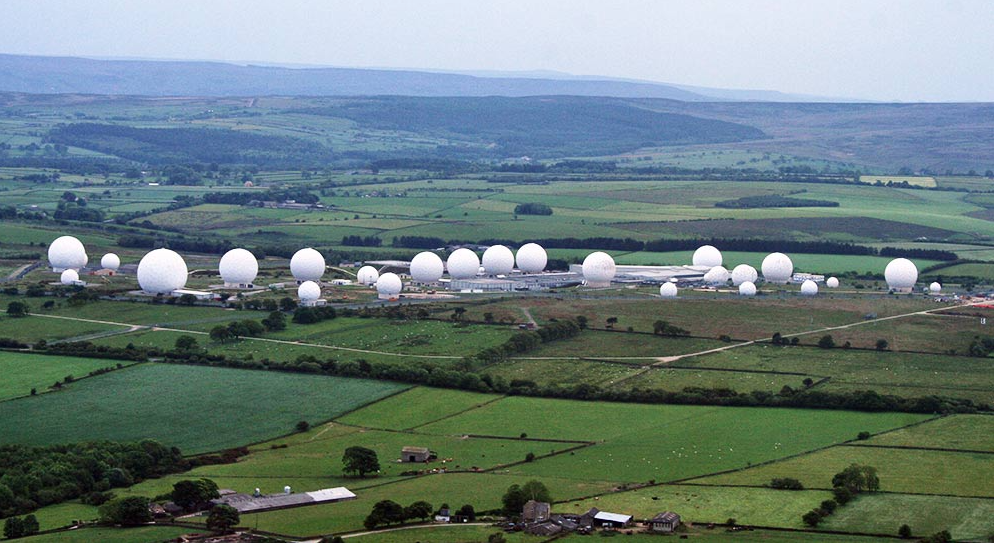
ECHELON was a Five Eyes surveillance network that intercepted virtually all satellite-based telephone, fax, and email communications worldwide. The European Parliament confirmed its existence in 2001 and condemned its use for corporate espionage, finding that the US and UK used ECHELON to steal contracts from European companies like Airbus.
Since 1988, the National Vaccine Injury Compensation Program has paid $5.4 billion to vaccine-injured individuals through a special 'vaccine court.' Of 28,292 petitions filed, 11,659 received compensation. The program is funded by a $0.75 tax on every vaccine dose. Despite compensating thousands of injuries, the program remains virtually unknown to the public. The CDC reports ~30,000 adverse events annually, yet only ~1,200 claims are filed each year — suggesting most injured people never learn the program exists.

HAARP (High-frequency Active Auroral Research Program) was initially funded by the US Air Force, Navy, and DARPA. It IS a real facility that uses high-powered radio signals to study the ionosphere for communications and surveillance. Hugo Chavez blamed it for the Haiti earthquake. However, experts including Stanford professor Umran Inan note its power is 'minuscule compared with a lightning flash' and it operates well above where weather forms. Since 2015 it has been run by the University of Alaska Fairbanks and hosts public open houses.
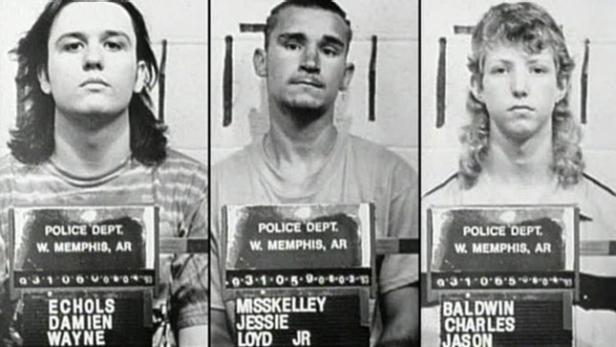
Arkansas prosecutors withheld evidence and relied on discredited forensic testimony to convict three teenagers for murder in 1993. DNA evidence and prosecutorial misconduct revelations led to their release through Alford pleas in 2011.

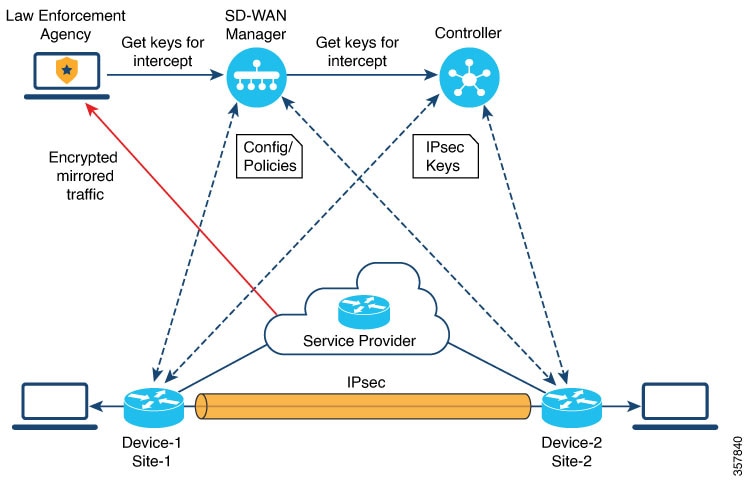
In 1993, the Clinton administration introduced the Clipper Chip (MYK-78), requiring all phones to include an NSA-designed encryption chip with built-in government backdoor access via key escrow. The encryption algorithm 'Skipjack' was classified, preventing peer review. In 1994, cryptographer Matt Blaze found a critical flaw that allowed the escrow system to be bypassed entirely. The chip was abandoned by 1996 after massive public opposition, but the concept of mandated encryption backdoors resurfaces regularly.

On June 8, 1967, Israeli forces attacked the clearly marked USS Liberty for over two hours, killing 34 American sailors and wounding 171. The ship was flying a large American flag. NSA recordings of the attack have suspicious blanks. The NSA deputy director called Israel's inquiry 'a whitewash.' Key documents remain classified over 50 years later despite survivors' demands for a full investigation.
Since the DOD's first-ever audit in 2018, it has failed every single year — 7 consecutive failures by 2024. The Pentagon cannot account for 63% of its $3.8 trillion in assets. In 2001, Secretary Rumsfeld admitted the Pentagon could not track $2.3 trillion in transactions. Pentagon money managers made $7 trillion in accounting adjustments to make ledgers 'add up,' but the Inspector General could not verify receipts for $2.3 trillion of those changes. The GAO has flagged this issue since 1981. Despite having an $824 billion annual budget, the DOD remains the only federal agency that has never passed a financial audit. Senator Warren called it 'the largest accounting fraud in history.'
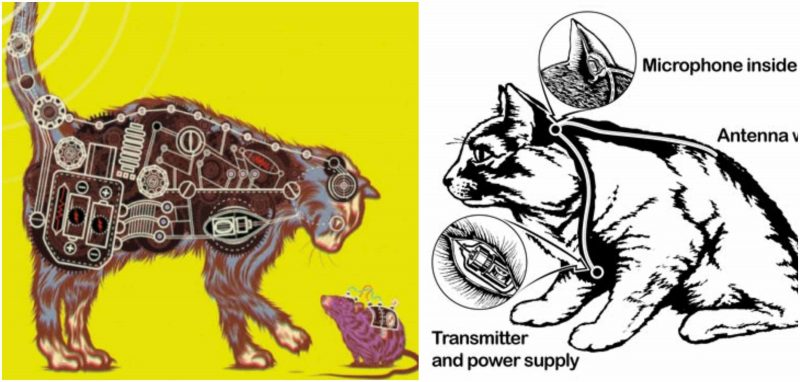
Declassified documents revealed CIA spent $20 million in 1960s surgically implanting listening devices and antennas in cats for espionage. The program was abandoned after operational failures.
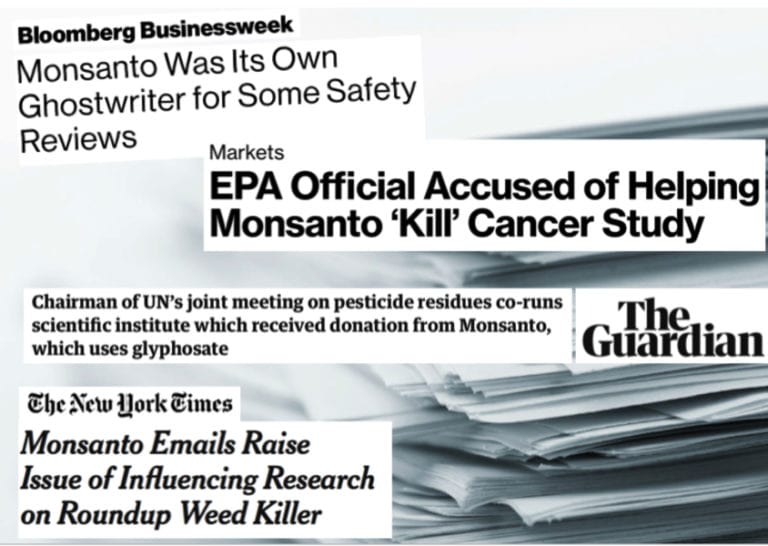
The 'Monsanto Papers' revealed that Monsanto's own toxicologist wrote in 2003: 'you cannot say that Roundup is not a carcinogen.' The company ghostwrote studies with academics as frontmen, launched coordinated attacks on IARC after its 'probable carcinogen' classification, and an EPA official boasted he could 'kill' an investigation and 'should get a medal.' A key safety study was retracted for 'serious ethical concerns.' Bayer (which acquired Monsanto) has paid over $10 billion in settlements.
In-Q-Tel, founded by the CIA in 1999, has invested in over 800 companies, funding technologies later used for mass surveillance. Its portfolio includes Palantir ($250B valuation), Keyhole Inc (became Google Earth), and Anduril. Much of its investment goes into data mining tools that collect and analyze social media data from Twitter, Facebook, and Instagram to monitor activists and 'decision-makers.' A Wall Street Journal investigation found nearly half of In-Q-Tel's trustees had financial connections to funded companies. Some investments remain classified.

2005: NSA historian Hanyok confirmed Aug 4, 1964 attack fabricated. Intel distorted. 58K Americans, 2-3M Vietnamese dead.

Before Edward Snowden's revelations in 2013, claims that the NSA was monitoring millions of Americans' communications were widely dismissed as paranoid speculation. The PRISM program and bulk metadata collection were confirmed through classified documents leaked by Snowden.

Snowden 2013: PRISM = '#1 raw intel source,' 91% of internet traffic. 120M+ Verizon records. XKeyscore: 'nearly everything.'
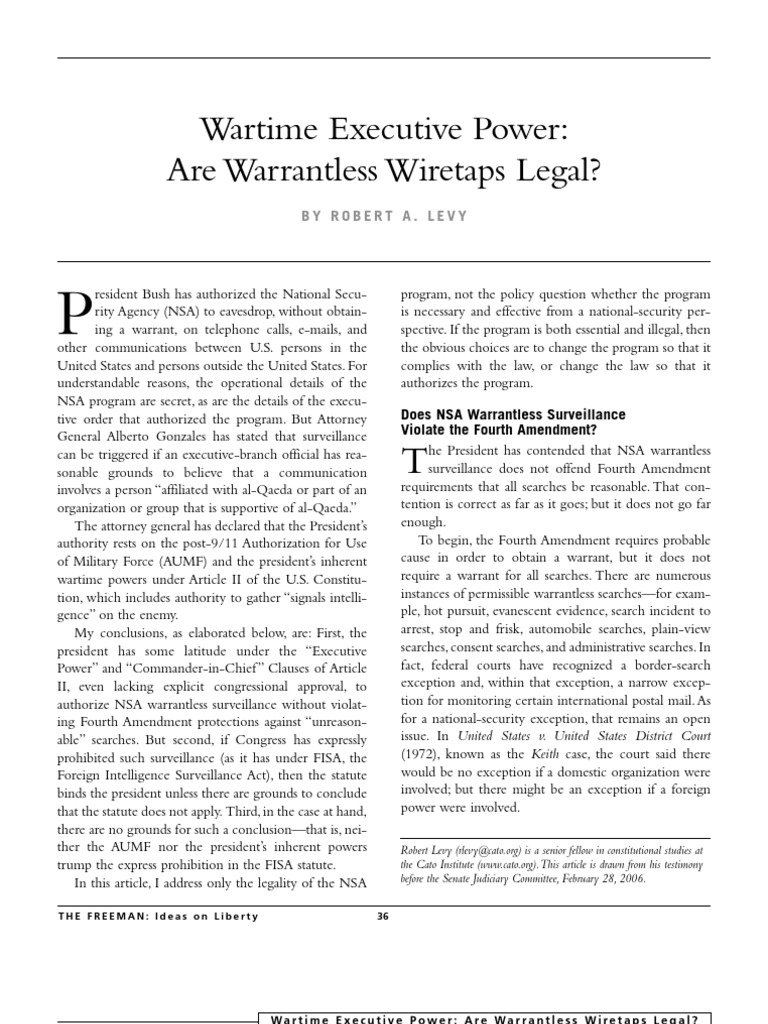
Bush administration claimed all surveillance was legal, but whistleblowers revealed NSA collected domestic communications without warrants from 2001-2006.
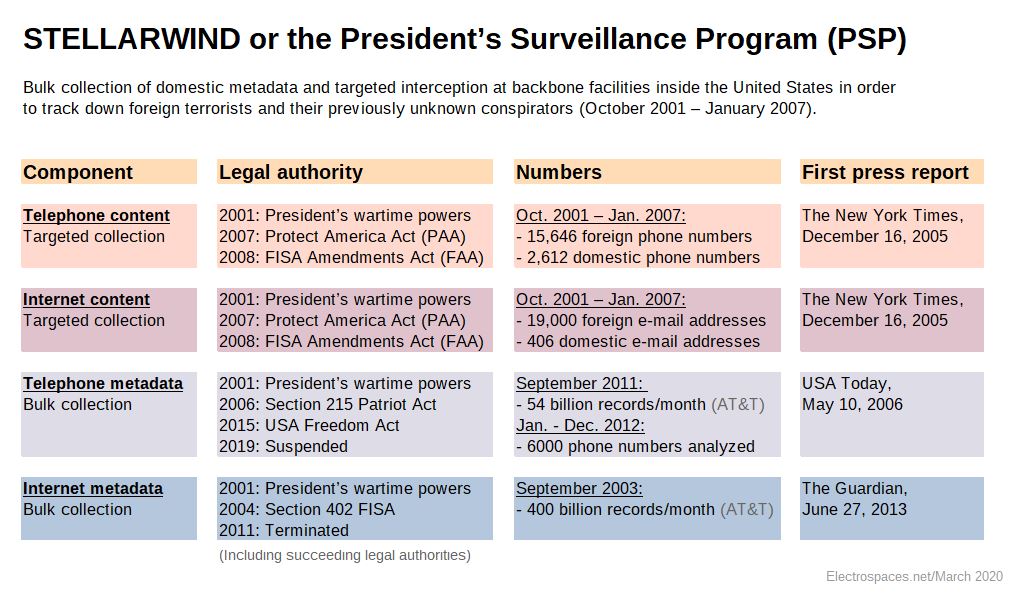
Before the Patriot Act, the NSA secretly collected bulk phone records and internet metadata starting in 2001 without legal authority.
Bush administration authorized NSA to monitor Americans' communications without court warrants after 9/11. Program operated in secret until exposed by New York Times in 2005.

AT&T secretly installed NSA surveillance equipment in San Francisco facility starting 2003. Whistleblower Mark Klein revealed fiber-optic splitters copying all internet traffic to government.

Former AT&T technician Mark Klein revealed that AT&T installed a secret room allowing NSA to intercept all internet traffic. Court documents and technical evidence confirmed the existence of this dragnet surveillance program.

In 2006, AT&T technician Mark Klein revealed that the NSA had installed fiber optic splitters in Room 641A at AT&T's San Francisco facility, copying all internet traffic passing through the building. The equipment could process 10 gigabits per second. Klein provided technical documents showing the setup was designed to intercept domestic communications without warrants. The EFF sued AT&T, and Congress later passed retroactive immunity for telecoms that cooperated.

Mark Klein, an AT&T technician for 22 years, discovered Room 641A at AT&T's San Francisco facility — a secret room where optical splitters created exact copies of all internet traffic passing through AT&T's backbone and redirected it to the NSA. The room contained a Narus STA 6400, capable of intercepting and analyzing internet communications at very high speeds. Klein went public in 2006 after reading about Bush's warrantless wiretapping program. The EFF filed Hepting v. AT&T, but Congress passed retroactive immunity for telecoms in 2008.

In 2002, Canadian citizen Maher Arar was detained at JFK Airport during a layover, rendered to Syria by the CIA, and tortured for nearly a year in a coffin-sized cell. A Canadian commission later confirmed he was completely innocent -- the RCMP had shared faulty intelligence with the US. Canada paid Arar $10.5 million in compensation. The US government never apologized and kept him on the no-fly list until 2009.

In January 2010, a 26-member Mossad team assassinated Hamas commander Mahmoud al-Mabhouh in a Dubai hotel room. Dubai police released full CCTV footage showing the entire operation: agents in disguises, surveillance, and the kill team. The agents used forged passports from the UK, Australia, Ireland, France, and Germany, leading those countries to expel Israeli diplomats in retaliation.

Wachovia, then the fourth-largest U.S. bank, failed to apply anti-money laundering controls to $378.4 billion in transactions from Mexican currency exchange houses between 2004-2007. At least $110 million in confirmed drug proceeds were laundered, including money used to buy drug-running airplanes. Despite the largest money laundering case ever brought against a U.S. bank, Wachovia paid just $160 million -- less than 2% of its 2009 profit -- and no executives faced charges.
Federal investigation revealed Wachovia processed drug money through casa de cambio transfers. Bank executives failed to monitor obviously suspicious large cash transactions.

Stuxnet, discovered in 2010, was a sophisticated malware designed to sabotage Iran's nuclear program by targeting Siemens SCADA systems controlling uranium enrichment centrifuges at Natanz. The classified 'Olympic Games' program, begun under Bush and continued under Obama, was confirmed by Snowden in 2013 as a US-Israel joint operation. Stuxnet destroyed approximately 1,000 centrifuges by manipulating their spin speeds while displaying normal readings to operators. It escaped into the wild and was detected by Kaspersky Lab researchers.

Stuxnet was a joint NSA-Mossad cyberweapon that destroyed approximately 1,000 Iranian nuclear centrifuges at the Natanz enrichment facility while displaying normal readings to operators. A Dutch mole working for the CIA and Mossad physically planted the malware. The operation, codenamed 'Olympic Games,' set Iran's nuclear program back by an estimated two years and established the precedent for nation-state cyber warfare.
HSBC, Europe's largest bank, was caught allowing drug kingpins including El Chapo's Sinaloa Cartel and Colombia's Norte del Valle Cartel to launder at least $881 million through its accounts. The bank failed to monitor over $670 billion in wire transfers and $9.4 billion in cash purchases from HSBC Mexico. Despite admitting to the crimes, HSBC received a deferred prosecution agreement -- paying $1.9 billion with no criminal charges against any executive.
A network of automated license plate readers (ALPRs) mounted on police cars, streetlights, and highway overpasses captures billions of license plate scans annually, building detailed movement profiles of virtually every driver. Private company Flock Safety has created a de facto nationwide surveillance system, running all plates against FBI databases. NYPD used ALPRs to spy on Muslims at mosques. Data shows disproportionate deployment in communities of color. 100% of departments serving 1M+ residents use the technology.
A 2012 Senate investigation found HSBC had laundered at least $881 million for Mexican and Colombian drug cartels, processed transactions for sanctioned nations including Iran and North Korea, and facilitated $15 billion in bulk cash transactions with Mexico. The bank paid a $1.9 billion fine — about five weeks of revenue — and entered a deferred prosecution agreement. No executives were criminally charged, prompting outrage about 'too big to jail.'
HSBC deliberately processed $881 billion in suspicious transactions for Mexican drug cartels and sanctioned countries. Internal documents showed executives knew about the money laundering but prioritized profits over compliance.

Whistleblower emails revealed the bank disguised Iranian wire transfers to evade sanctions. Executives called regulators 'fucking Americans' and prioritized profits over compliance.

Standard Chartered processed $250 billion in Iranian transactions while US sanctions were in effect. They stripped identifying information from wire transfers and used Dubai operations to conceal Iranian origins from American authorities.

Trader communications showed UBS employees rigged the London Interbank Offered Rate. Internal messages revealed systematic manipulation affecting trillions in global transactions.

On March 12, 2013, Senator Ron Wyden asked DNI James Clapper: 'Does the NSA collect any type of data at all on millions of Americans?' Clapper answered 'No sir... not wittingly.' Three months later, Edward Snowden's leaks proved this was a lie. Clapper later called it the 'least untruthful' answer he could give. Despite committing perjury before Congress, Clapper was never charged and continued serving until 2017.
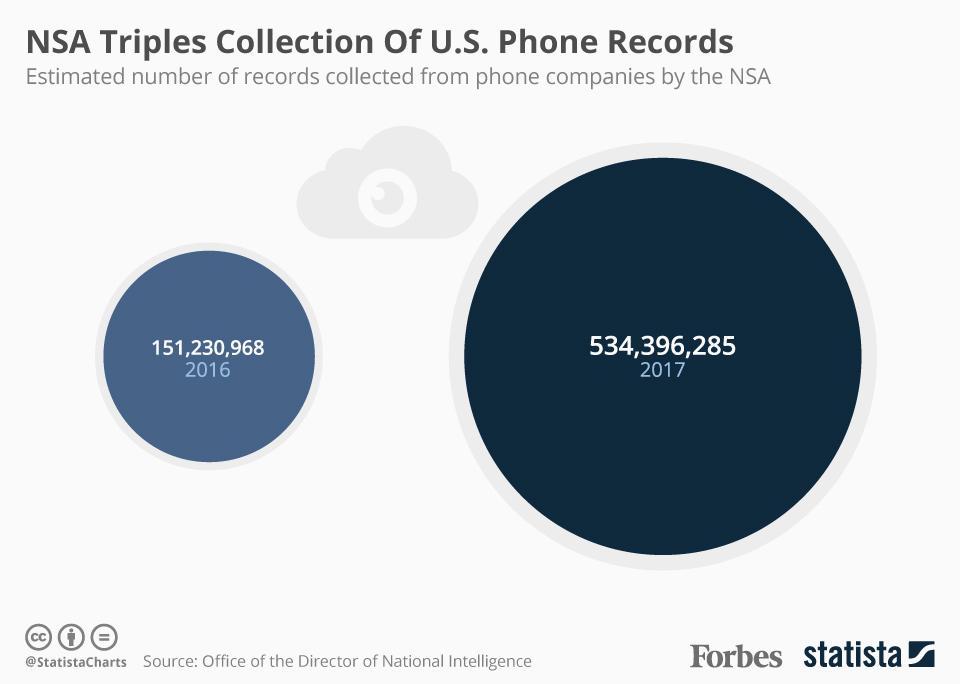
Snowden's first major revelation exposed the NSA's bulk collection of telephone metadata — every call made by every American — under Section 215 of the Patriot Act. A secret FISA court order required Verizon to hand over all call records 'on an ongoing daily basis.' In 2015, a federal appeals court ruled the program was illegal, stating Congress never authorized such sweeping collection. The USA FREEDOM Act of 2015 officially ended bulk collection, but the revelation shattered trust in intelligence oversight.
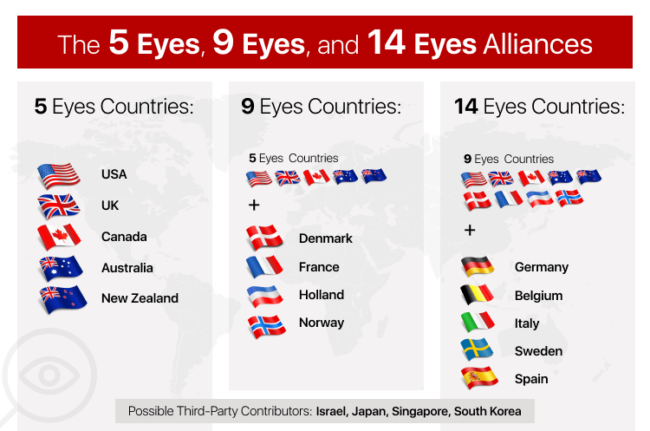
Snowden documents confirmed the long-suspected arrangement where Five Eyes alliance members (US, UK, Canada, Australia, New Zealand) share intelligence to bypass their own domestic surveillance restrictions. GCHQ collects data on Americans and shares it with the NSA, while the NSA does the same for British citizens — allowing each to claim they are not spying on their own people. The UKUSA Agreement formalized this arrangement, and the Tempora and MUSCULAR programs demonstrated the data-sharing pipeline in practice.
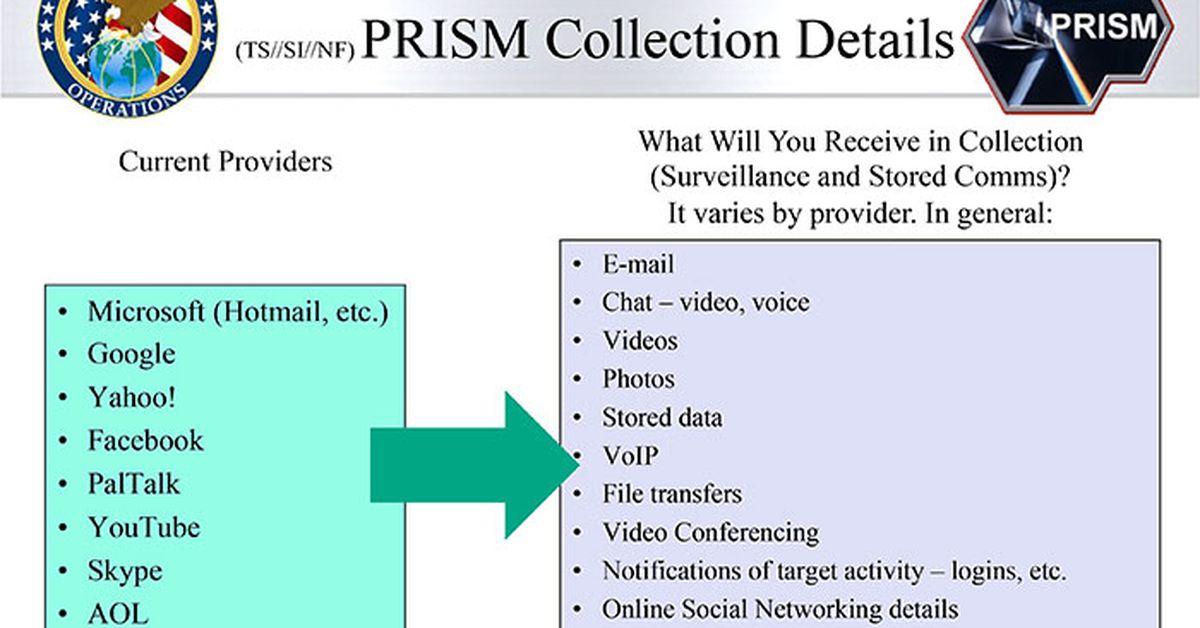
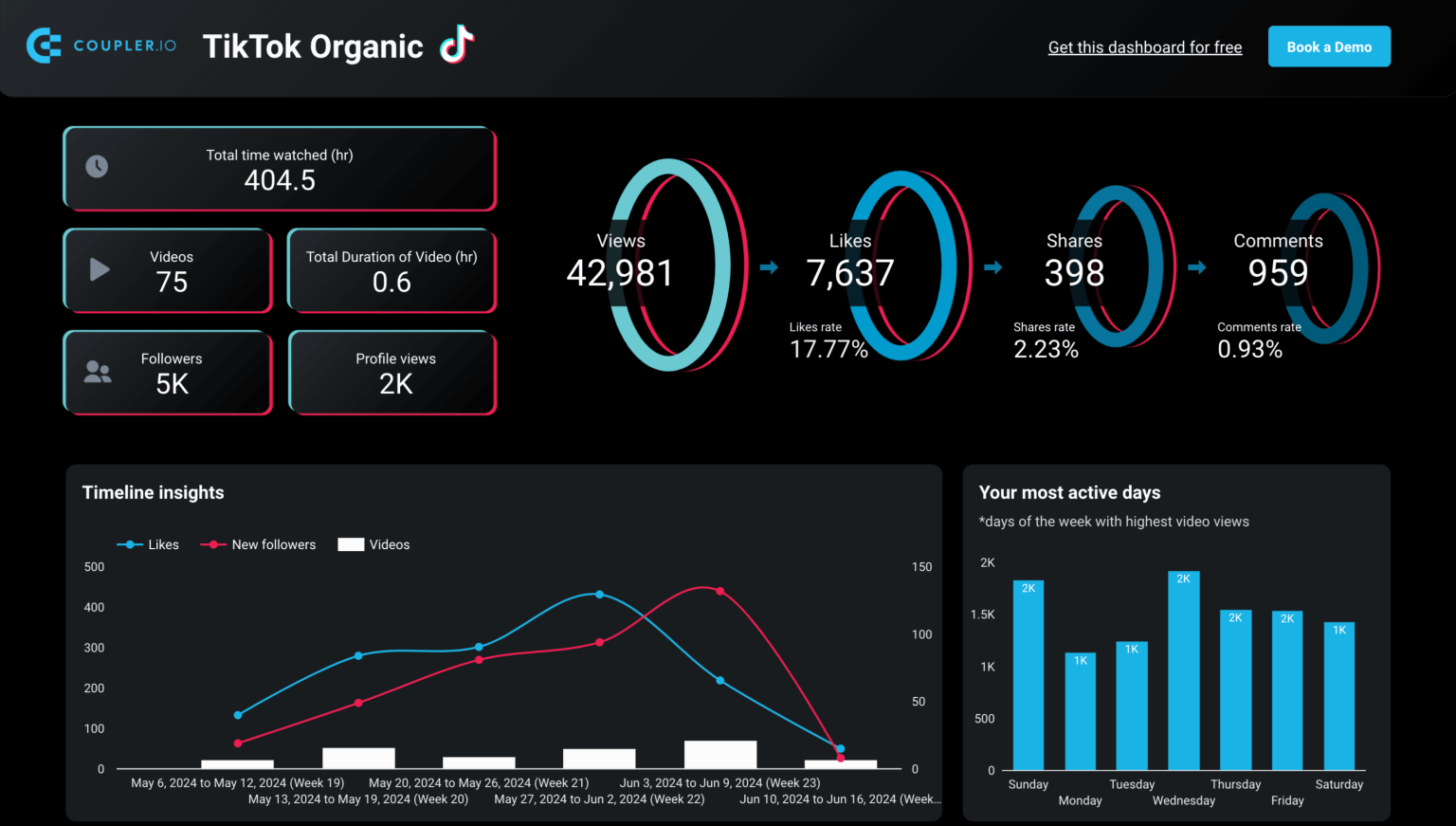
Edward Snowden revealed that the PRISM program gave the NSA direct access to the servers of nine major tech companies. PRISM was 'the number one source of raw intelligence used for NSA analytic reports,' accounting for 91% of internet traffic acquired under FISA Section 702. The Boundless Informant tool showed over 97 billion pieces of intelligence collected in a single 30-day period.

Between 1979 and 2012, the Foreign Intelligence Surveillance Court received 33,900 surveillance requests and denied only 11 — a 99.97% approval rate. The court operates in total secrecy with no adversarial process. Declassified opinions revealed the FBI used Section 702 to surveil a sitting state court judge who had complained about civil rights violations by a police chief. The court has been called 'the most one-sided legal process in the United States.'

Snowden revealed the NSA's capability to remotely activate a target's phone microphone and camera, even when the device appears to be powered off. The CIA's Vault 7 leaks confirmed similar capabilities. The NSA's DROPOUTJEEP tool, documented in the ANT Catalog, provided 'software implant for the Apple iPhone that utilizes modular mission applications to provide SIGINT functionality' including remote control of the microphone and camera. A 100% success rate was claimed for iPhone implants. Similar tools existed for Android devices.

Between 1979 and 2012, the Foreign Intelligence Surveillance Court received 33,900 surveillance requests and denied only 11 - a 99.97% approval rate. The court operates in total secrecy with no adversarial process. Declassified opinions revealed the FBI used Section 702 to surveil a sitting state court judge who had complained about civil rights violations by a police chief.
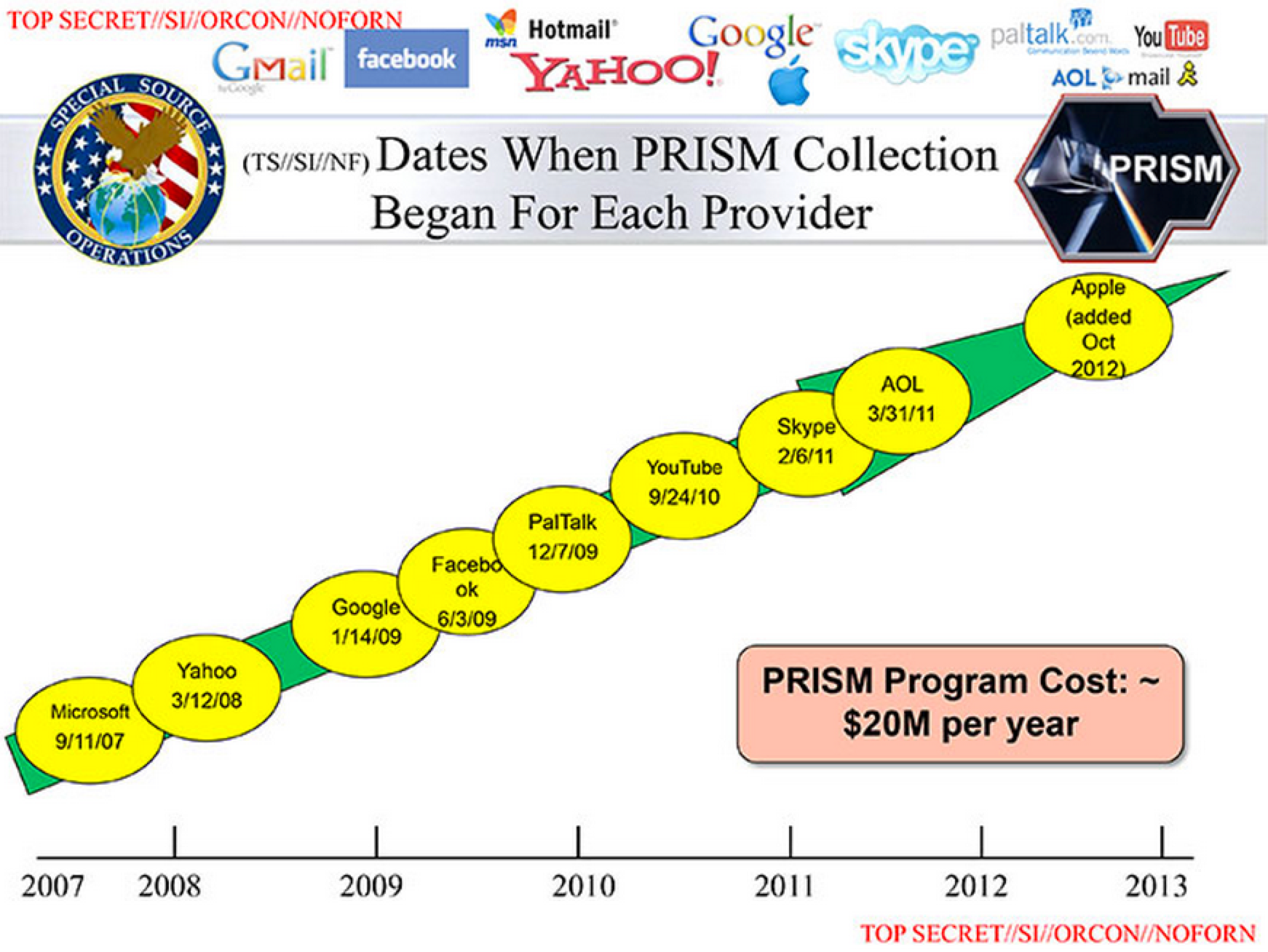
Edward Snowden's 2013 leak revealed PRISM, a secret NSA program operational since 2007 under the Protect America Act. PRISM granted the NSA direct access to the servers of nine major tech companies — Google, Facebook, Apple, Microsoft, Yahoo, Skype, YouTube, AOL, and PalTalk — allowing the agency to collect emails, chats, photos, and stored data without users' knowledge. Intelligence chief James Clapper had told Congress the NSA was 'not wittingly' collecting data on Americans, a statement proven false.
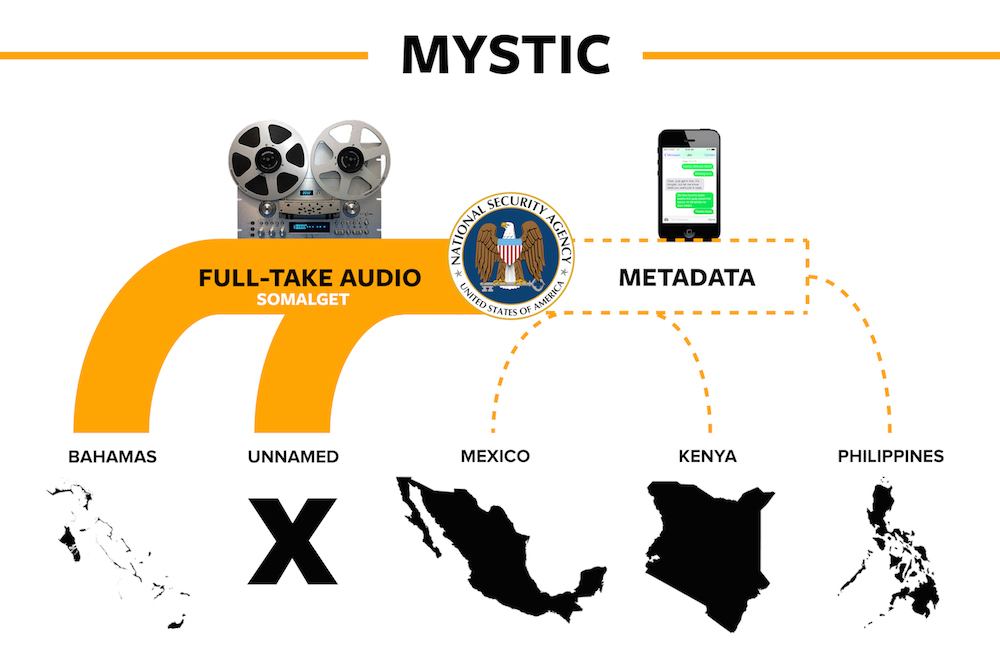
Edward Snowden's leaks revealed the NSA's MYSTIC program could record 100% of a foreign country's telephone calls for 30-day rolling periods through its RETRO tool. The Washington Post confirmed the program captured actual voice content, not just metadata as officials had claimed. The program operated in at least five countries. This went far beyond the 'just metadata' assurances given to Congress and the public.
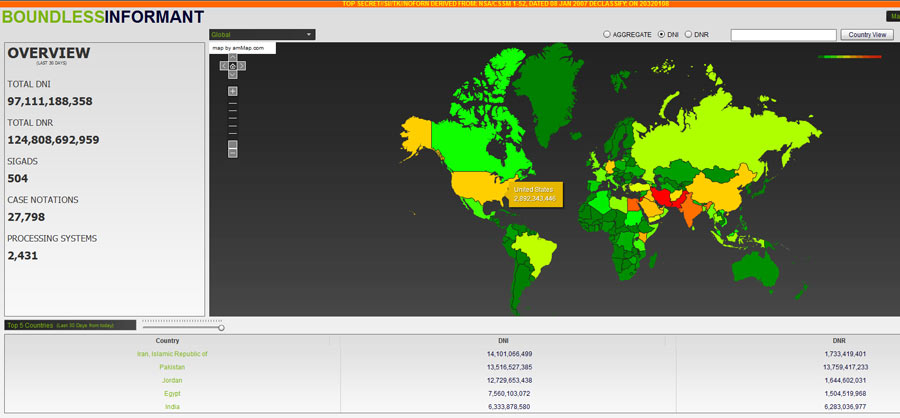
Snowden leaked details of Boundless Informant, an NSA data visualization tool that counted and categorized metadata collected globally. In March 2013 alone, the NSA collected 97 billion pieces of intelligence from computer networks worldwide, with Iran (14 billion), Pakistan (13.5 billion), and Jordan (12.7 billion) being top targets. The tool's existence directly contradicted NSA Director Keith Alexander's testimony to Congress that the NSA did not have the ability to determine how much data it collects on Americans.
Snowden's 2013 revelations exposed XKeyscore, an NSA system enabling analysts to search virtually anyone's internet activity — emails, browsing history, social media, chats — using just a name, email address, phone number, or even keywords, all without prior judicial authorization. Training materials described it as the 'widest-reaching' system for searching through internet data. The NSA collected over 20 billion communication events per day worldwide.

Snowden documents revealed Tempora, a GCHQ program operational since late 2011, which intercepted data from fiber-optic cables forming the backbone of the internet. GCHQ placed intercepts on over 200 cables, each carrying 10 gigabits per second, buffering content for 3 days and metadata for 30 days. The data was shared with the NSA. At its peak, GCHQ was processing 600 million 'telephone events' per day. The program operated under secret legal interpretations that were never publicly debated or approved by Parliament.
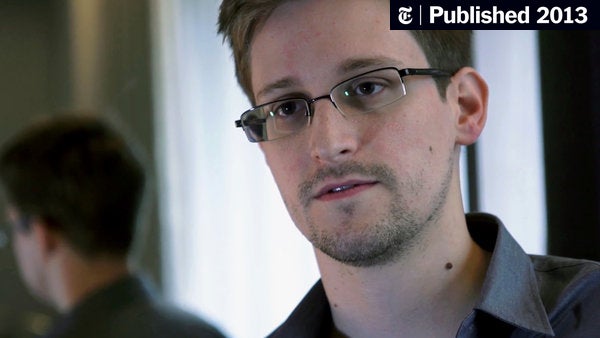
Edward Snowden was charged under the Espionage Act of 1917, which was designed for spies selling secrets to foreign governments. The Act provides no mechanism for a 'public interest' defense — meaning at trial, Snowden would be legally prohibited from explaining why he leaked or arguing that revealing illegal mass surveillance served the public. The programs he exposed were later ruled unconstitutional by federal courts, and Congress passed the USA FREEDOM Act reforming NSA surveillance. Despite this vindication, Snowden remains in exile in Russia.

GCHQ denied improper surveillance, but Snowden documents revealed UK intelligence bypassed domestic restrictions by sharing data through NSA programs.

Edward Snowden documents revealed Microsoft provided NSA with backdoor access to Skype communications and Outlook.com emails. The PRISM program allowed surveillance despite encryption claims.
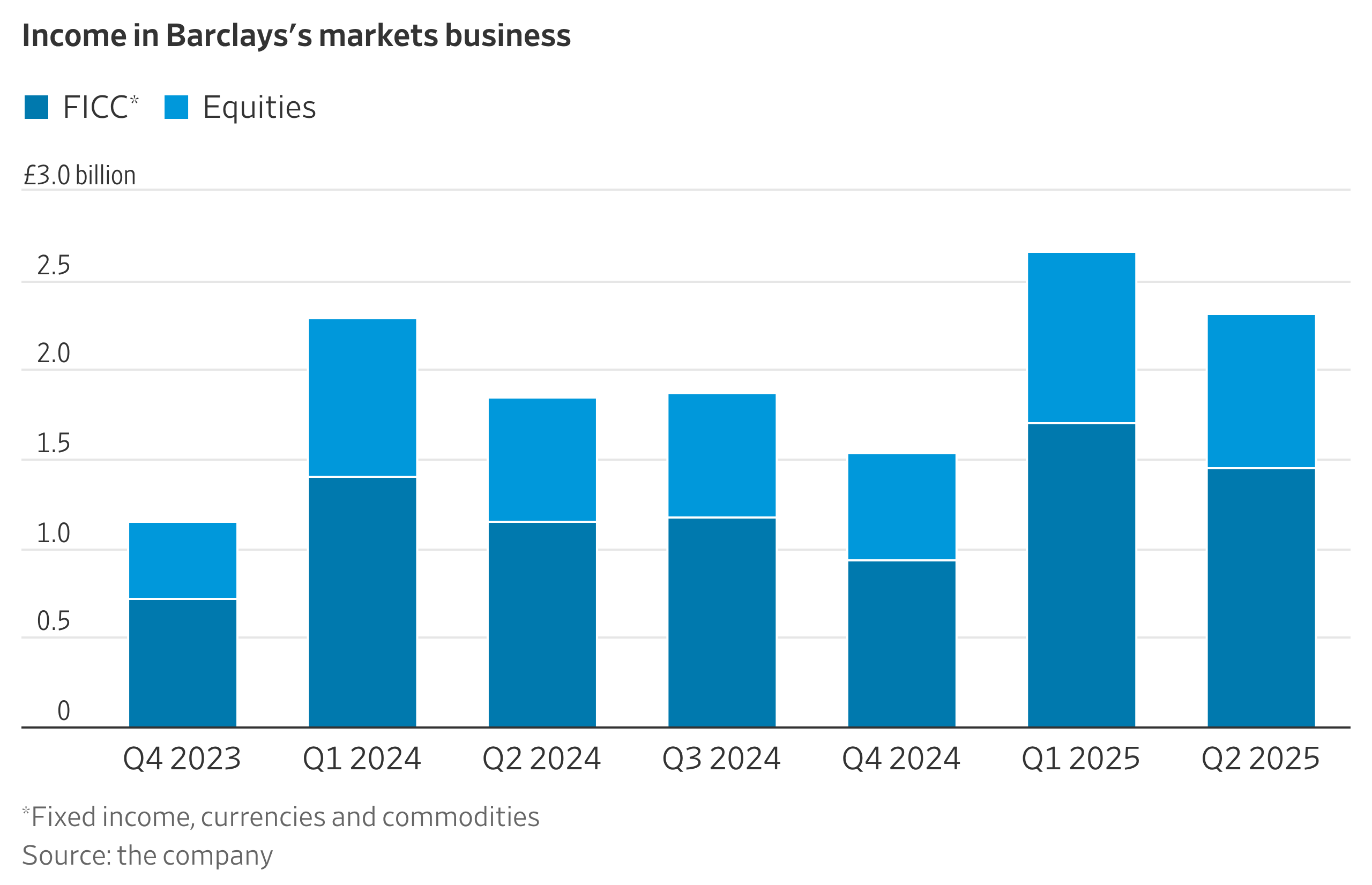
FERC investigation revealed Barclays submitted false power transaction data to manipulate price indices. Traders coordinated to move markets and increase profits on derivative positions.
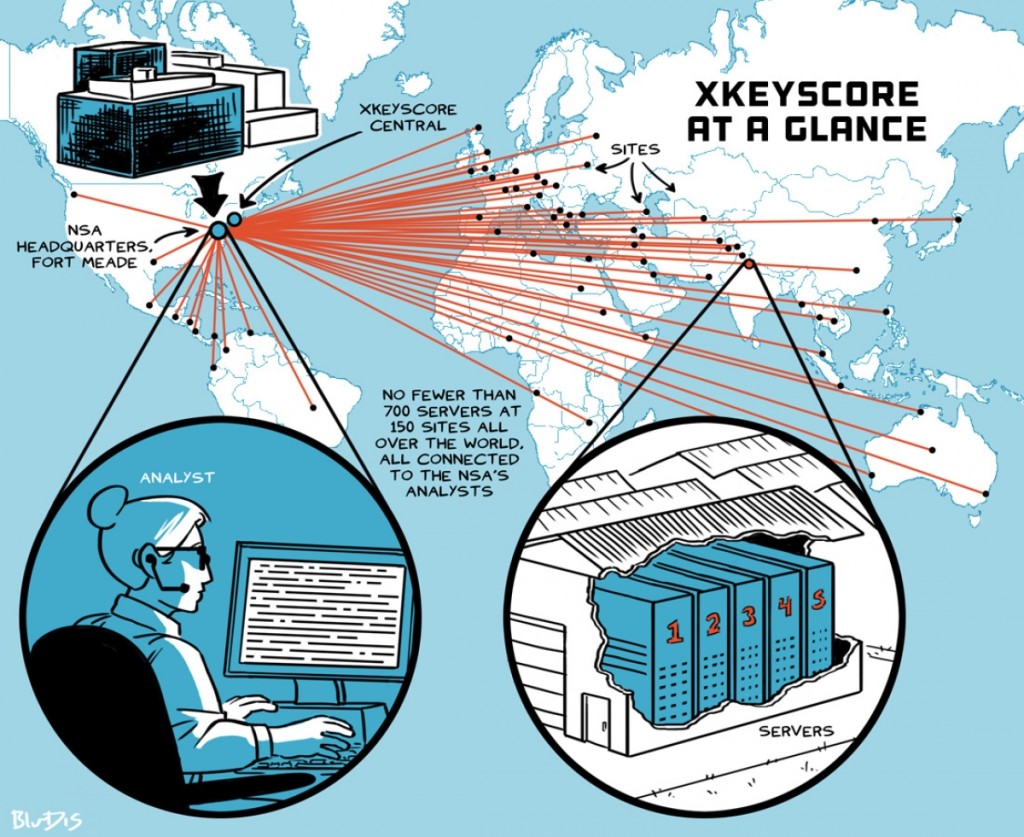
XKeyscore is an NSA system that allows analysts to search through vast databases of emails, online chats, and browsing histories of millions of individuals without prior authorization or a warrant. Training materials showed analysts needed only fill out a simple on-screen form giving a broad justification. The system was shared with intelligence agencies from Australia, Canada, New Zealand, Britain, Japan, Germany, and Denmark.

Reuters revealed in 2013 that the DEA's Special Operations Division instructs agents to practice 'parallel construction' — recreating the investigative trail to conceal that evidence originated from NSA warrantless surveillance. Agents fabricate alternative explanations for how they found suspects, essentially laundering illegally obtained evidence into court-admissible form. Defense attorneys are never told the true origin of evidence, violating defendants' constitutional rights. The practice has never been successfully challenged in court.

Reuters revealed in 2013 that the DEA's Special Operations Division instructs agents to practice 'parallel construction' - recreating the investigative trail to conceal that evidence originated from NSA warrantless surveillance. Agents fabricate alternative explanations for how they found suspects, essentially laundering illegally obtained evidence into court-admissible form. The practice has never been successfully challenged.

The DEA's Special Operations Division used NSA surveillance to build drug cases but instructed agents to create false evidence trails. This 'parallel construction' violated due process rights.

The DEA's Special Operations Division used NSA intelligence to build cases, then created false evidence chains to hide the illegal surveillance sources.
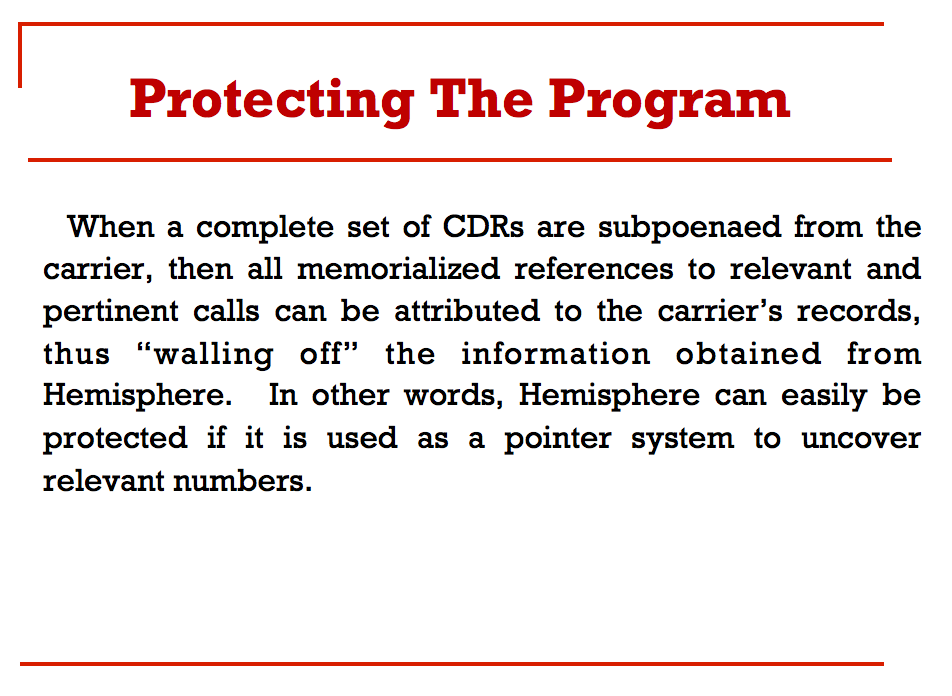
The DEA's Special Operations Division used 'parallel construction' to hide NSA intelligence sources in criminal prosecutions. Internal documents showed agents were instructed to create false investigative trails to conceal surveillance origins.

The Hemisphere Project, revealed in 2013, gives the DEA access to a database of every phone call that has passed through an AT&T switch since 1987 - over 4 billion records per day, dwarfing the NSA's metadata program. AT&T employees are embedded in DEA offices to run searches. The program specifically instructs agents to never reveal Hemisphere as the source of information and to use parallel construction to hide its existence.

Snowden documents revealed the MUSCULAR program (DS-200B), jointly operated by the NSA and GCHQ, which intercepted data flowing through fiber-optic cables connecting Google and Yahoo data centers worldwide. Unlike PRISM, MUSCULAR required no warrants or corporate cooperation. In just 30 days, the program collected over 181 million records including emails, text, audio, and video. Google was so outraged it began encrypting all inter-data-center traffic.

Reuters revealed RSA took payment from NSA to make NSA's flawed Dual_EC_DRBG the default in their software. Internal NSA documents showed the algorithm contained a backdoor for surveillance.

Der Spiegel revealed that the NSA's Tailored Access Operations (TAO) unit, comprising over 1,000 hackers, intercepts computer equipment during shipping to implant hardware and software backdoors before delivery to the target. The NSA's ANT catalog lists dozens of implant tools for routers, servers, and firewalls from major manufacturers. The practice undermines global trust in US technology products.
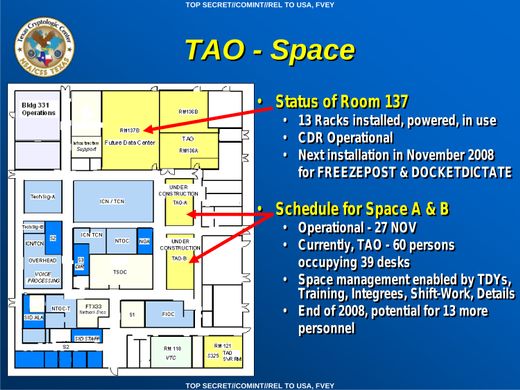
Der Spiegel revealed in 2013, from Snowden documents, that NSA's Tailored Access Operations (TAO) unit routinely intercepted servers, routers, and networking equipment during shipping to install covert hardware implants and firmware backdoors before delivery. The ANT Catalog listed 100+ products including radio frequency modules, firmware Trojans, and tools targeting Cisco, Juniper, Huawei, and Apple devices. TAO's 'load stations' would open packages, install surveillance equipment, reseal them, and send them to targets. The unit hacked 258 targets across 89 countries.
Der Spiegel revealed NSA's ANT catalog showing how agency intercepted Cisco router shipments to install surveillance backdoors. Photos showed NSA employees opening sealed packages before delivery.
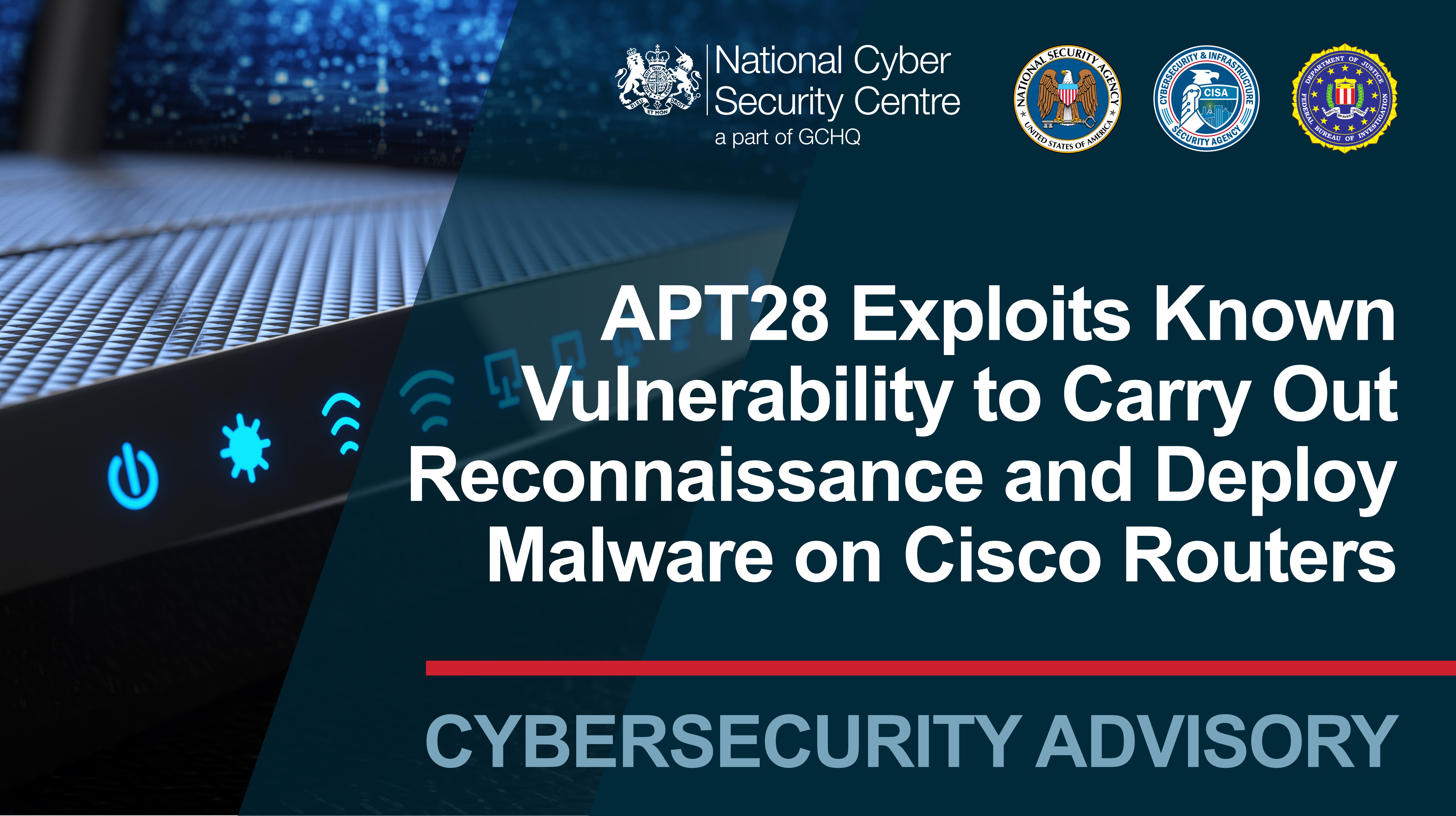
Leaked NSA documents revealed Tailored Access Operations intercepted Cisco equipment to install backdoors. Company products were compromised before reaching customers.
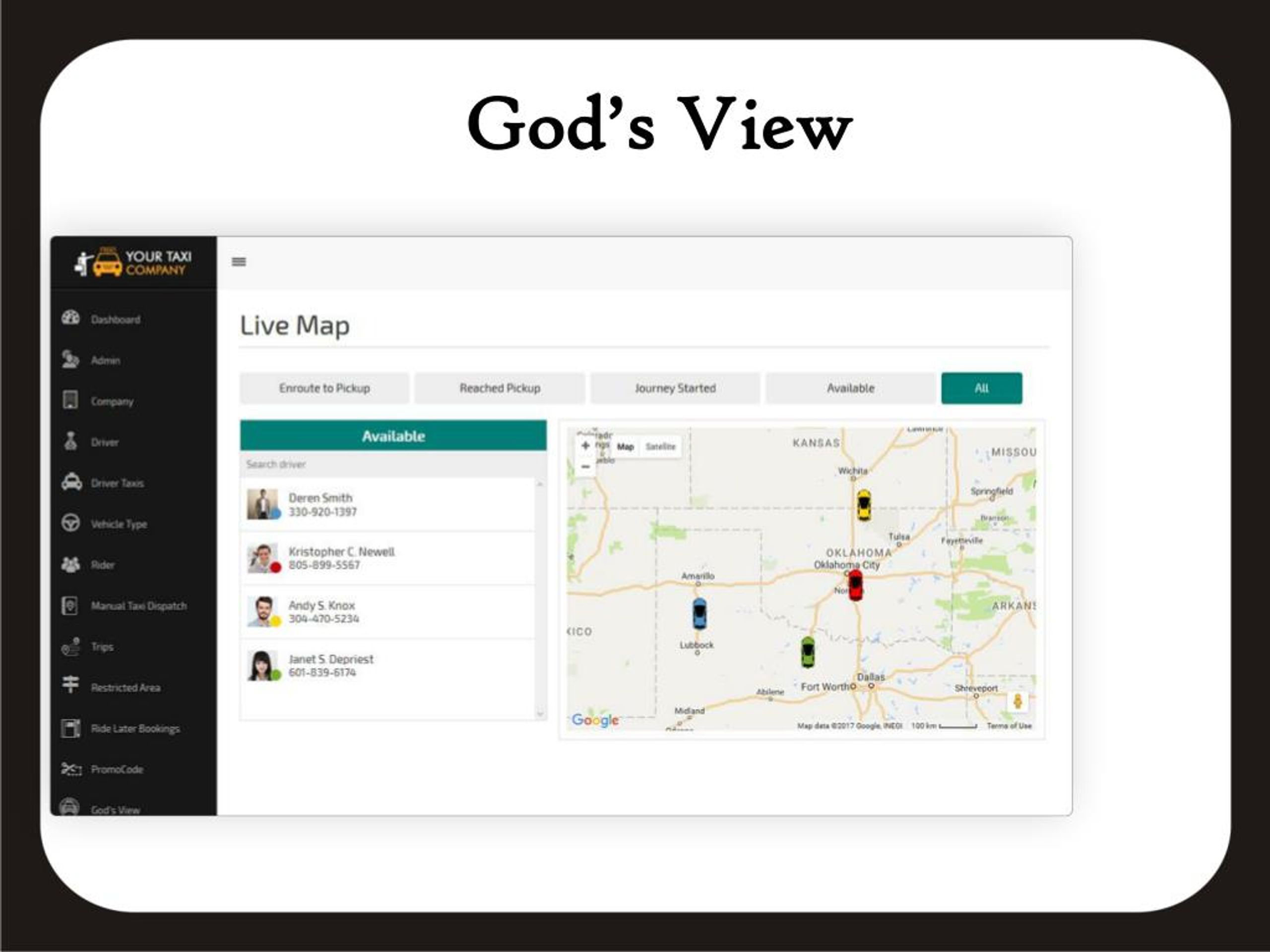
Uber had an internal surveillance tool called 'God View' that tracked the real-time location of all Uber vehicles and customers. In November 2014, Uber's NYC general manager Josh Mohrer tracked BuzzFeed reporter Johana Bhuiyan without permission, greeting her with 'I was tracking you.' In 2011, a venture capitalist's live Uber trip was displayed on a big screen at an Uber launch party in Chicago without his knowledge. Executive Emil Michael suggested investigating journalists critical of Uber. God View was available to corporate employees company-wide. The NY Attorney General fined Uber $20,000.

Internal Monsanto documents ('Monsanto Papers') revealed the company ghostwrote scientific studies, attacked independent researchers, and colluded with EPA officials to suppress findings linking glyphosate to cancer. The WHO's IARC classified glyphosate as 'probably carcinogenic' in 2015. Bayer (which acquired Monsanto) has paid over $16 billion to settle over 100,000 Roundup cancer lawsuits, mostly non-Hodgkin lymphoma cases.
Internal emails revealed Monsanto employees ghostwrote scientific papers and paid academics to sign them. Company knew glyphosate might cause cancer but published studies claiming safety.

BND denied improper data sharing, but parliamentary investigation revealed German intelligence provided NSA with European communications data for over a decade.

The FBI operates a fleet of small aircraft equipped with dirtbox technology (IMSI catchers more powerful than Stingrays) that can intercept phone data from thousands of phones simultaneously. The planes are registered to at least 13 fictitious companies created by the FBI to hide ownership. They were observed flying over more than 30 cities in 11 US states in a single 30-day period, conducting warrantless mass surveillance.
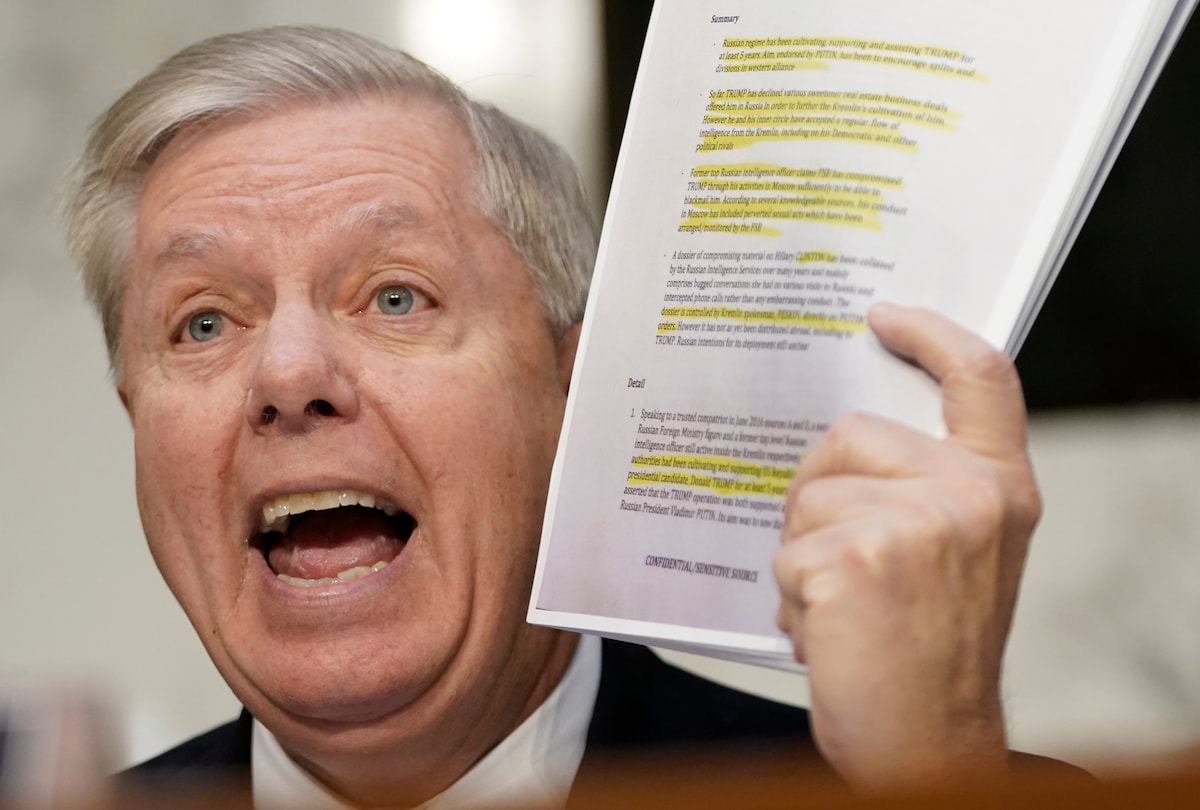
The Steele Dossier, funded by the Clinton campaign through Fusion GPS, was treated as credible by major outlets. BuzzFeed published it in full in January 2017. CNN, MSNBC, and the Washington Post built years of coverage around its claims. The FBI used it to obtain FISA warrants to surveil Trump campaign advisor Carter Page. Durham found the FBI offered Steele $1 million for corroboration — he provided none. Multiple Dossier claims were debunked: the alleged Prague meeting never happened, and key source Igor Danchenko was charged with lying to the FBI.

Deutsche Bank processed $20 billion in suspicious Russian transactions through coordinated trades between Moscow and London. Internal compliance officers flagged the scheme for years but executives ignored warnings to maintain profitable relationships.

Palantir Technologies, backed by CIA venture fund In-Q-Tel, built surveillance platforms used by ICE since 2013 (FALCON, ICM) for workplace raids, tracking asylum seekers, and large-scale immigration enforcement. In 2025, ICE awarded Palantir $30M to build 'ImmigrationOS,' a platform using data from passports, Social Security, IRS, and even Medicaid records to identify and track deportation targets. Palantir's ELITE tool uses Medicaid data to locate individuals, generating 'confidence scores' for current addresses.
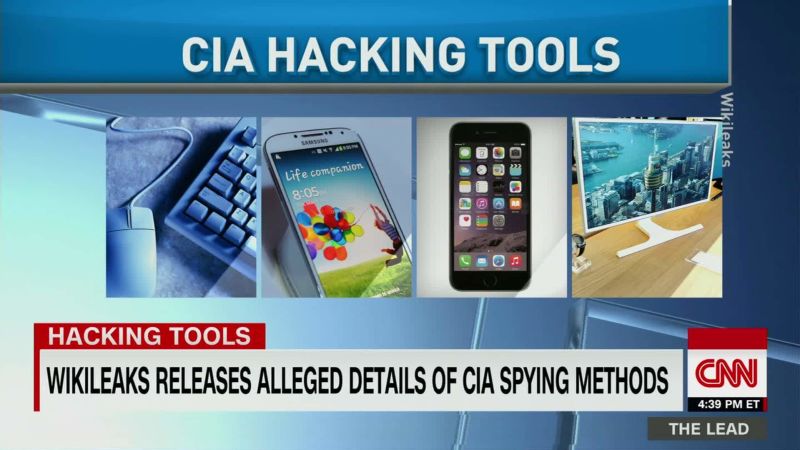
WikiLeaks' 2017 Vault 7 release exposed the CIA's arsenal of cyber weapons. 'Weeping Angel,' co-developed with MI5, turned Samsung smart TVs into covert listening devices using a 'Fake Off' mode that made TVs appear powered down while secretly recording audio. The CIA's Mobile Devices Branch could remotely hack iPhones and Android phones, activating cameras and microphones. Other tools targeted car computer systems, which WikiLeaks noted could be used for 'nearly undetectable assassinations.'

Court documents revealed Monsanto employees ghostwrote scientific papers on glyphosate safety then recruited academics to sign as authors, while internally discussing cancer risks they publicly denied.
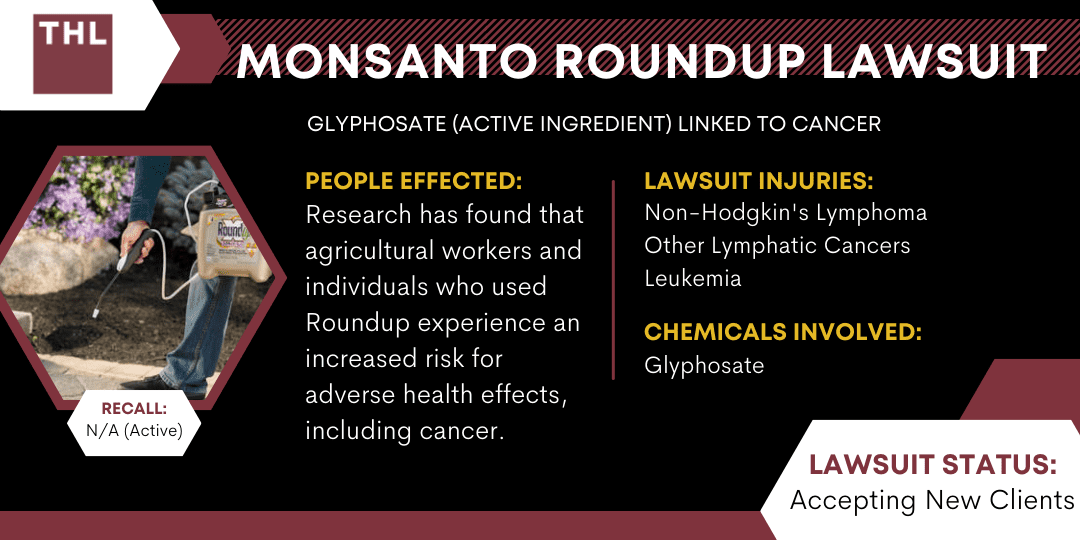
Court filings in 2017 revealed Monsanto employees ghost-wrote supposedly independent research papers and suppressed internal studies showing glyphosate's potential cancer links since the 1980s.

Court documents revealed Monsanto employees ghostwrote research papers published under academic scientists' names claiming glyphosate safety while internal emails showed cancer concerns.

Court documents from Roundup litigation revealed Monsanto knew about potential cancer risks from glyphosate since the 1980s. Company ghost-wrote studies and pressured scientists to avoid cancer classifications.

Court documents from 2017 showed Monsanto employees secretly authored supposedly independent research and knew about potential cancer links since 1980s.

Internal Monsanto emails revealed company scientists ghostwrote academic papers and paid researchers to publish studies downplaying glyphosate cancer risks. The WHO classified glyphosate as a probable carcinogen in 2015.

Internal Monsanto emails revealed the company wrote scientific papers concluding Roundup 'does not pose a health risk' then paid outside scientists to sign as authors. A Monsanto executive wrote that scientists would 'have their names on the publication, but we would be keeping the cost down by us doing the writing.' In 2015, scientist William Heydens suggested they 'ghost-write' another paper with Monsanto paying scientists to 'edit & sign their names.' The landmark Williams et al. (2000) paper was cited by government agencies worldwide for two decades before being retracted in November 2025 for 'serious ethical concerns.'

AUSTRAC investigation found CBA's systems failed to monitor deposits under $10,000 designed to avoid reporting. Money laundering and terrorism financing went undetected for years.

Internal Monsanto emails revealed company scientists ghostwrote academic papers defending glyphosate safety and worked to suppress studies showing cancer links.

In 2017, Google partnered with the Pentagon on Project Maven, using AI to analyze drone surveillance footage and identify targets. The contract was kept secret until exposed by Gizmodo in March 2018. Over 4,000 Google employees signed a letter demanding Google exit 'the business of war,' and at least 12 resigned in protest. Google eventually let the contract expire in March 2019 and published AI ethics principles prohibiting weapons development. Palantir subsequently took over the contract.

Bayer acquired Monsanto in 2018 for $63 billion, inheriting devastating Roundup cancer litigation. The company has already spent over $10 billion resolving cases with 65,000 claims still pending. Bayer's legal strategy includes pushing for a $7.25 billion class settlement, arguing federal preemption to block future claims, and threatening to put Monsanto into bankruptcy protection. In Missouri, Bayer spent two years lobbying for legislation to shield it from lawsuits. They've stopped making glyphosate Roundup for home use and are seeking approval for a replacement herbicide.
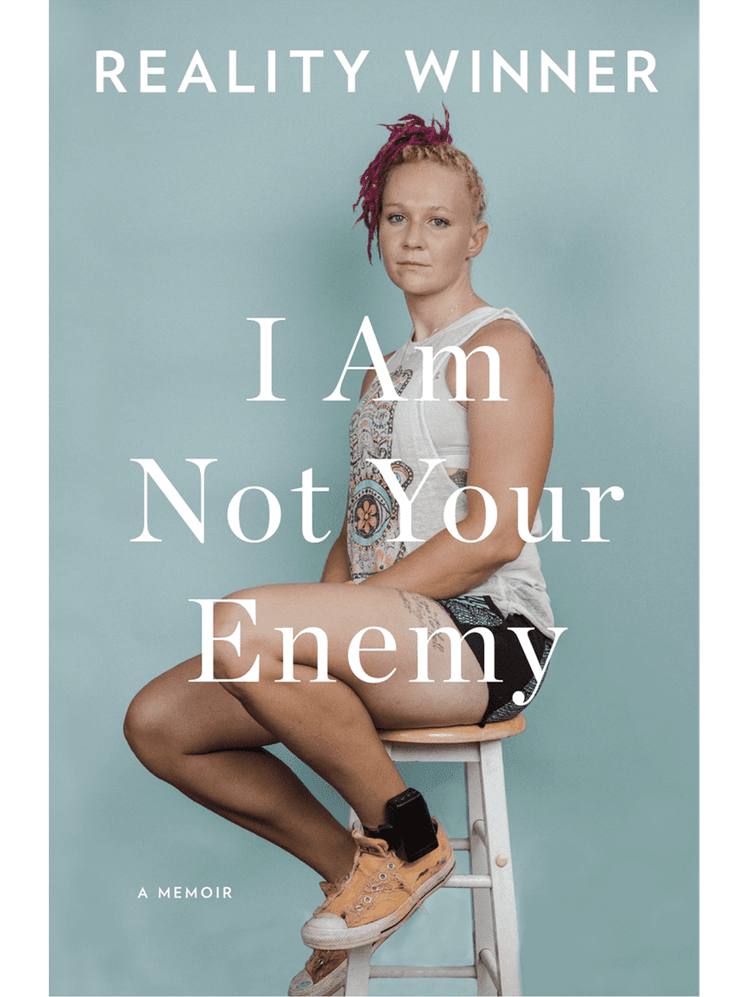
NSA translator Reality Winner leaked a single classified document to The Intercept showing Russian military intelligence attempted to hack US voting software companies before the 2016 election. She received 5 years and 3 months — the longest sentence ever imposed for an unauthorized disclosure to the media. By contrast, General Petraeus received probation for sharing highly classified information with his biographer/mistress, and Sandy Berger received a fine for stealing classified documents from the National Archives.

Danske Bank's Estonian branch processed €200 billion in suspicious transactions from Russia and former Soviet states. Internal whistleblower Howard Wilkinson revealed executives knew about the money laundering but prioritized profits.
The rise in seed oil consumption has paralleled dramatic increases in obesity, heart disease, diabetes, and autoimmune conditions. Published research shows omega-6 polyunsaturated fat linoleic acid promotes oxidative stress, oxidised LDL, and chronic inflammation. The omega-6 to omega-3 ratio in Western diets shifted from 1:1 to as high as 20:1. Yet major health institutions continue to recommend seed oils as 'heart healthy,' often citing industry-funded research. The debate over seed oils vs. traditional fats remains aggressively suppressed.

Amazon's Ring doorbell cameras created a distributed surveillance network of over 10 million devices. Amazon disclosed to Congress that it shared Ring footage with police at least 11 times in 2022 without a warrant or the owner's consent, using a self-defined 'emergency' exception. Police used the Neighbors app to request footage en masse, and Ring footage was used to monitor protesters. After EFF and ACLU pressure, Ring ended the police request feature in January 2024, but emergency disclosures continue.
After JPMorgan distanced itself from Epstein in 2013, Deutsche Bank opened 40+ accounts for the convicted sex offender. For five years, the bank processed millions in suspicious transactions including payments to women labeled 'tuition fees,' cash withdrawals structured to avoid reporting, and transfers to individuals publicly alleged to be Epstein's co-conspirators. Compliance officers raised concerns in 2015 but management overruled them. Deutsche Bank was fined $150 million and paid $75 million to victims -- total cost: $350+ million.

On August 9-10, 2019, Jeffrey Epstein was found dead in his cell at the Metropolitan Correctional Center. Guards Tova Noel and Michael Thomas didn't check on him for 8 hours, shopped online, and falsified logs. Both surveillance cameras outside his cell malfunctioned — 10 of 11 cameras in the SHU were not recording. His cellmate was transferred the day before. Dr. Michael Baden, hired by the family, found the hyoid bone fractures were more consistent with strangulation than hanging. The guards accepted plea deals to avoid prison.

On Feb 13, 2020, Intel Committee Chair Richard Burr sold $628K-$1.7M across 33 transactions. On Feb 7, he wrote 'the US is better prepared than ever.' On Feb 27, he privately told donors it was 'much more aggressive than anything we have seen.' FBI seized his phone; DOJ dropped charges Jan 2021.

Jan 24, 2020: same day as briefing, Loeffler and NYSE chairman husband sold $1.275M-$3.1M across 27 transactions while buying Citrix (telework). DOJ dropped probe May 2020.
FinCEN found TD Bank processed $1.2 billion in transactions for Scott Rothstein's Ponzi scheme without filing required suspicious activity reports. Internal systems flagged concerns but were ignored.

134 countries (98% of global GDP) are developing CBDCs that would give central banks unprecedented visibility into every financial transaction. China's digital yuan already feeds data into its social credit system -- by 2019, over 26 million air ticket purchases were blocked for 'untrustworthy' citizens. CBDCs could impose restrictions on purchases, set expiration dates on currency, apply personalized inflation rates, or freeze accounts instantly. Multiple U.S. senators have introduced legislation to ban a CBDC in America.
Concerns about CBDCs as government surveillance tools went from fringe to mainstream policy. Congress introduced the 'CBDC Anti-Surveillance State Act' and in May 2024 passed legislation prohibiting the Federal Reserve from issuing a CBDC without congressional approval. China's integration of social surveillance with its digital yuan validated privacy fears. The European Data Protection Supervisor flagged CBDCs as a major privacy concern, and multiple countries paused CBDC development over surveillance risks.

Bank records showed Deutsche Bank processed suspicious transactions for Epstein for years. Internal compliance officers flagged concerns but executives overruled them for profits.
In August 2021, Apple announced a system to scan all photos uploaded to iCloud using NeuralHash to detect CSAM. Security researchers and the EFF immediately warned it was 'a backdoor masquerading as child safety' that governments could exploit to search for political content. Over 5,000 organizations and individuals signed an open letter opposing it. Apple delayed the rollout, then quietly killed the project in December 2022, admitting that scanning users' photos 'would create new threat vectors for data thieves' and open the door to 'bulk surveillance.'
A declassified September 2021 federal watchdog report revealed the NSA continued to violate key rules limiting warrantless searches of Americans' electronic communications. The FBI was found to have improperly searched NSA data for information on Americans in hundreds of thousands of cases. The FBI also used small aircraft registered to fictitious companies with video and cellphone surveillance technology, observed over 30 cities in 11 states in just 30 days.
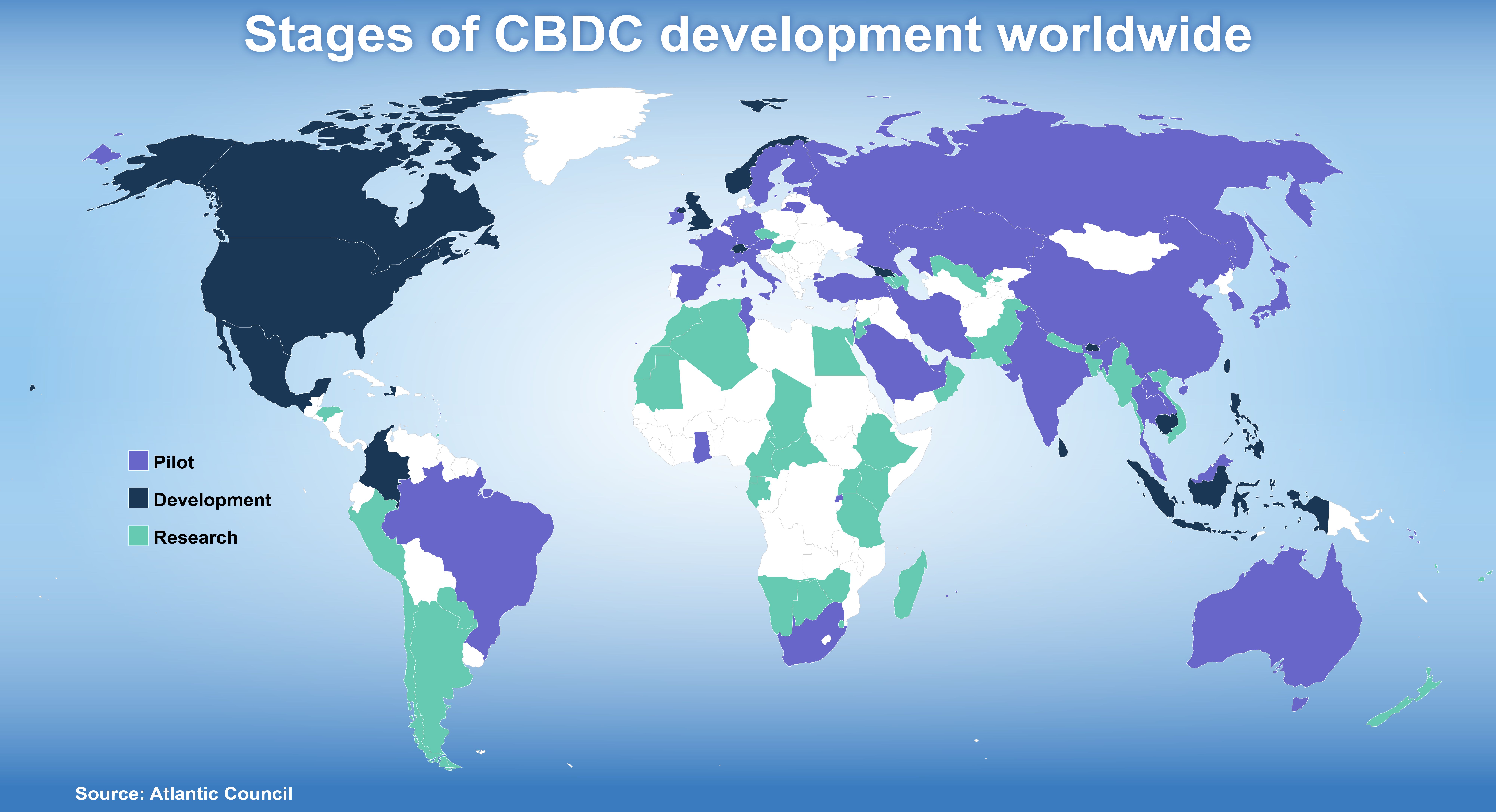
As of 2024, 134 countries representing 98% of global GDP are exploring Central Bank Digital Currencies. China's digital yuan (e-CNY) already allows the government to monitor transactions in real-time, set expiration dates on money, and restrict purchases. The ECB's digital euro proposal includes potential spending limits and transaction monitoring. Nigeria's eNaira was linked to a cashless policy that caused widespread protests. Privacy advocates warn CBDCs could enable governments to freeze accounts, implement negative interest rates, and create financial social credit systems.
The US government pushed to ban TikTok citing national security concerns about Chinese data collection. Critics point out that US companies like Meta and Google collect identical or more extensive data on American users, share it with advertisers, and have been caught providing it to law enforcement without warrants. The RESTRICT Act proposed to address TikTok would grant sweeping surveillance powers far beyond the app. Former NSA Director Keith Alexander sits on the board of Amazon, which collects vast amounts of user data. The real concern appears to be a foreign government having data access that the US government wants to control.

Security researchers discovered that the official White House mobile app has OneSignal SDK compiled in, which polls user GPS coordinates every 4.5 minutes and syncs them to a third-party server.
Federal agencies including the FBI, ICE, and CBP routinely purchase Americans personal data from commercial data brokers, circumventing Fourth Amendment protections against warrantless surveillance.

In 2024, Congress reauthorized and expanded FISA Section 702, which allows intelligence agencies to conduct warrantless surveillance of Americans' communications. The expansion broadened the definition of 'electronic communication service provider,' potentially forcing any business with access to communications equipment to assist in surveillance.

CBDCs being developed by central banks worldwide would give governments the ability to track every transaction, freeze accounts instantly, and program money with expiration dates or spending restrictions.

The European Parliament voted to reject Chat Control, which would have mandated mass scanning of all private messages. Germany's Friedrich Merz expressed 'deep disappointment' and announced plans to implement equivalent surveillance at the national level by summer.

Hong Kong amended its national security law to make it a criminal offense to refuse to provide passwords to personal mobile devices when demanded by authorities. The US Consulate issued a security alert to American citizens.

Documents in the Epstein files contain a claim that the Kremlin funneled approximately $100 million to Donald Trump through Florida real estate transactions. The story received 17,800 upvotes on Reddit but minimal mainstream coverage.
NPR reported that the Trump administration's DHS is linking data across multiple federal agencies to build a national citizenship tracking tool. The system would create a comprehensive database tracking the citizenship status of everyone in the United States.

FBI Director Kash Patel confirmed at a Senate Intelligence Committee hearing that the FBI actively purchases commercially available location data to track Americans — no warrant required. The admission was reported by The Guardian, TechCrunch, Ars Technica, and NPR.

An investigation by WIRED revealed that Microsoft, Amazon, Google, and Palantir collectively spent at least $515 million providing surveillance technology to ICE and CBP — including iris scanners, facial recognition, phone-hacking software, and cell location tracking.

Four executives were sentenced to 126 years in prison for using Israeli-made Predator spyware to illegally surveil 87 people including politicians and journalists. The convicted spyware dealer now claims the Greek government was behind the entire operation.

A report revealed that Meta's Ray-Ban smart glasses are sending video footage — including content flagged as 'sensitive' — to human data annotators in Kenya for labeling. Content that was supposed to be automatically excluded is being reviewed by low-paid workers overseas.

Senate investigation reveals Apollo co-founder Leon Black paid Epstein $170M (30x market rate for 'tax advice'), funneled $20M in hush money through Epstein, and that Epstein + Paul Weiss chairman ran physical surveillance operations against women on Black's behalf.

LinkedIn injects a 2.7MB JavaScript bundle that silently scans for 6,000+ Chrome extensions — including ones revealing religion, political orientation, and neurodivergence. Then fingerprints your hardware. No disclosure, no opt-out.

Internal DHS documents reveal AI-powered autonomous surveillance trucks, 198 AI camera towers, contracts with spyware firms Cellebrite and Paragon, and a $1B Palantir data fusion platform — all funded by $191B from the 'One Big Beautiful Bill.'

Federal ICE agents were photographed wearing Meta Ray-Ban AI smart glasses during immigration raids — enabling real-time facial recognition, silent video recording, and biometric tracking of entire neighborhoods without consent or warrants.

The official White House app pings users' GPS location to an outside server every 4.5 minutes and requests fingerprint scanner and internal storage access. No transparency about who operates the third-party server.

Meta announced it will remove end-to-end encryption from Instagram direct messages starting May 2026, making billions of private conversations readable by the company, advertisers, and law enforcement.

ICE said agents were attacked with a shovel for 3 minutes before shooting. City surveillance video shows a 12-second scuffle. The shovel was dropped before it started. Federal criminal probe opened.
Russia blocked VPNs, throttled Telegram, and mandated state super-app 'Max' on every phone sold since Sept 2025. Max has no end-to-end encryption and shares data directly with the FSB.

Peter Thiel's Palantir CEO publicly discussed the company's role in undermining democratic institutions and consolidating surveillance power. Not a leak — an open confession.

Two senior MOD systems engineers went public saying Palantir built 'a rich picture of our nation' through 670M+ in UK government contracts including the nuclear weapons agency. 13 former US Palantir employees also signed a whistleblower letter.
A Connecticut insurance company denied a homeowner's storm damage claim using historical aerial images, arguing damage pre-existed. Insurers increasingly use satellite surveillance to find reasons to deny claims without site visits.
DNI Tulsi Gabbard and FBI preparing a 'large body of declassified evidence' on foreign election interference AND a surveillance program that targeted Americans using 'speech delimiters' — flagging communications based on language markers.

Switzerland officially ended its Palantir contract over data sovereignty risks. When the country that trusts nobody and stores everyone's secrets says your surveillance company is too risky, that's a signal.

A leaked Palantir ELITE user guide instructed operators to disable eligibility filters to maximize surveillance targets. Oregon federal court testimony confirmed ICE used Medicaid enrollment records to identify and select raid locations.
A group calling itself 'Department of Peace' leaked 17 megabytes of internal DHS procurement files identifying 6,681 companies contracting with ICE and DHS on surveillance programs. The group cited federal killings of Minneapolis protesters as motive.

Salt Typhoon, a hacking group linked to Chinese intelligence, infiltrated the FBI's DCSNet/DCS-3000 wiretap infrastructure and obtained the phone numbers of individuals under active federal surveillance. The FBI declared a major cyber incident under FISMA.

A recorded tape of Palantir CEO Alex Karp surfaced in April 2026 in which he describes people killed in Gaza as 'mostly terrorists' and Palestinian civilians as 'useful idiots.' UK Members of Parliament described his published manifesto as 'ramblings of a supervillain' and called for review of Palantir's NHS data contract and UK government agreements.

A class-action lawsuit targets San Jose, its police, and Flock Safety over a network of 500 automated license plate readers that log every vehicle in the city, with data accessible to ICE and FBI without warrants.

The DOJ opened a $40 million victim compensation claim process for OneCoin — one of the largest fraud schemes in history at $4 billion. Co-founder Ruja Ignatova, known as the 'Cryptoqueen,' has been on the FBI Most Wanted list since 2022 and remains at large.
A declassified NSA Inspector General report, obtained by POGO via FOIA, confirms multiple analysts illegally queried U.S. persons' communications outside Section 702 authorization. One self-reported after weeks of unauthorized queries; a second was caught by post-query audit.
Leaked DHS policy documents describe a 'Masked Engagement' program authorizing thousands of agents to create fictitious online identities, befriend targets, and join private groups — used against pro-Palestine activists and Mexican-American communities with no defined legal limits.

A Border Patrol intel unit opened a profile on a U.S. citizen for posting a peaceful anti-ICE protest announcement to Reddit. Internal records show agents internally acknowledged no threat existed but continued surveillance under a 'Force Protection' classification.
Treasury Secretary Scott Bessent is coordinating a rollout requiring U.S. banks to collect citizenship data from all customers — effectively building a bank-level national citizenship registry without a single piece of standalone legislation.

Allen devoted multiple paragraphs to ridiculing the agency tasked with stopping him: 'If I was an Iranian agent, instead of an American citizen, I could have brought a damn Ma Deuce in here and no one would have noticed.' (A Ma Deuce is the M2 .50-caliber machine gun.) He called the lapse 'actually insane.'
Every entry on this timeline started as a tip. If you have documentation, a court filing, a leaked memo or a screenshot — drop it.
+ Drop a Receipt