Google admitted Street View vehicles collected passwords, emails, and personal data from unsecured WiFi networks. Company initially claimed only public information was gathered.
“Street View cars collect only publicly broadcast WiFi network names and MAC addresses to improve location services.”
From “crazy” to confirmed
The Claim Is Made
This is the moment they called it crazy.
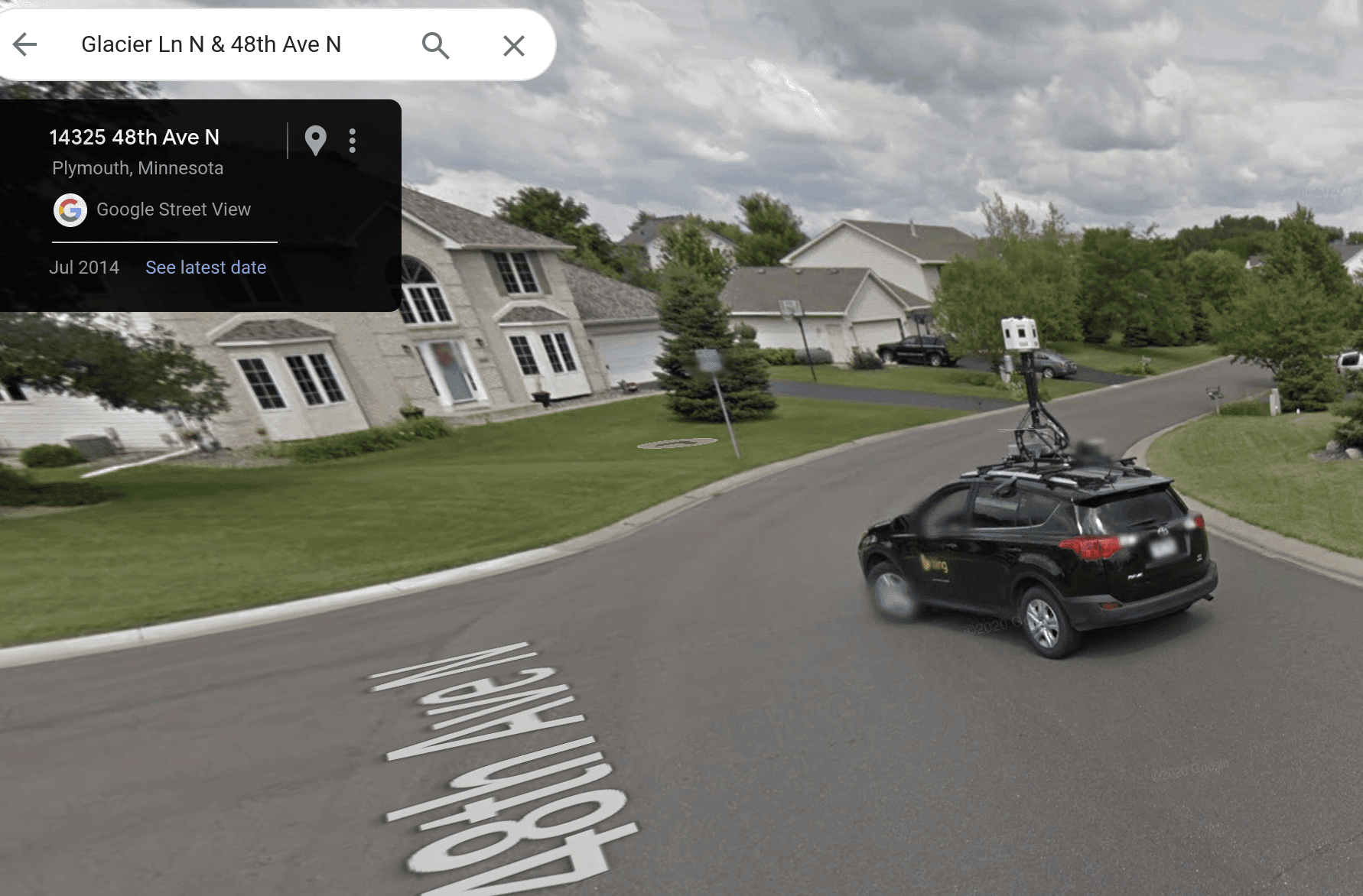
Between 2008 and 2010, Google sent thousands of Street View vehicles across the globe to photograph streets for its mapping service. These cars didn't just capture images. Unbeknownst to millions of people, they were also systematically collecting data from private WiFi networks.
Google's initial explanation was straightforward and reassuring. The company claimed its Street View vehicles only gathered information about publicly available WiFi networks—essentially, the names and signal strengths that any device could detect. There was nothing to worry about, Google said. No passwords, no emails, no personal information. Just public data collection as part of their mapping effort.
For years, this explanation satisfied regulators and the public. Street View became ubiquitous. The technology seemed benign, even helpful. Google had a reputation as the "don't be evil" company. Questions about data collection were dismissed as paranoia or misunderstanding.
Then came the investigation that changed everything. In 2010, German privacy regulators began examining what Google Street View vehicles had actually captured. What they found contradicted Google's public statements. The cars hadn't just collected WiFi network names. They had harvested passwords, email addresses, confidential business communications, and other sensitive personal information from unsecured networks. Some of this data collection appeared deliberate, embedded in the vehicle software rather than accidental.
Get the 5 biggest receipts every week, straight to your inbox — plus an exclusive PDF: The Top 10 Conspiracy Theories Proven True in 2025-2026. No spam. No agenda. Just the papers they couldn't hide.
You just read "Google Street View Cars Secretly Collected Private WiFi Data". We send ones like this every week.
No one's said anything yet. Be the first to drop your take.
Google's response shifted. The company acknowledged the data collection but reframed it as an unintended consequence of code designed for a different purpose. They called it a mistake. A programming error. Nothing malicious, just an oversight that slipped through during development.
Regulators weren't satisfied with this explanation. Multiple countries launched investigations. Germany's data protection authorities were particularly thorough, finding that Google had been collecting far more data than the company had acknowledged. The evidence was clear: Google Street View vehicles in Germany alone had captured thousands of passwords and other private information.
What makes this case remarkable isn't that a technology company made a mistake. It's how long the gap persisted between what Google claimed and what they were actually doing. For roughly two years, a false narrative protected the company from scrutiny while ordinary people's private information was being collected without their knowledge or consent.
Google eventually paid fines in multiple countries, though the amounts were modest relative to the company's resources. They apologized and implemented new privacy safeguards. The Street View program continued, simply with better constraints on what data vehicles could collect.
The lasting significance of this case extends beyond Google. It established a pattern: tech companies make claims about data collection practices that later prove incomplete or misleading. When discovered, these aren't typically prosecuted as fraud. They're described as accidents or misunderstandings. Fines are levied. Apologies are issued. Operations continue.
For those who paid attention, the Street View incident revealed something important about corporate accountability in the tech industry. A company's public reassurances aren't guarantees. Regulators in one country might catch what others miss. And privacy violations, when uncovered, often result in consequences far smaller than the violations themselves.
The question remains relevant today: what aren't we being told about the data currently being collected?
Beat the odds
This had a 1% chance of leaking — someone talked anyway.
Conspirators
~150Network
Secret kept
16 years
Time to 95% exposure
500+ years